Journal of Jilin University(Engineering and Technology Edition) ›› 2025, Vol. 55 ›› Issue (12): 4024-4033.doi: 10.13229/j.cnki.jdxbgxb.20240437
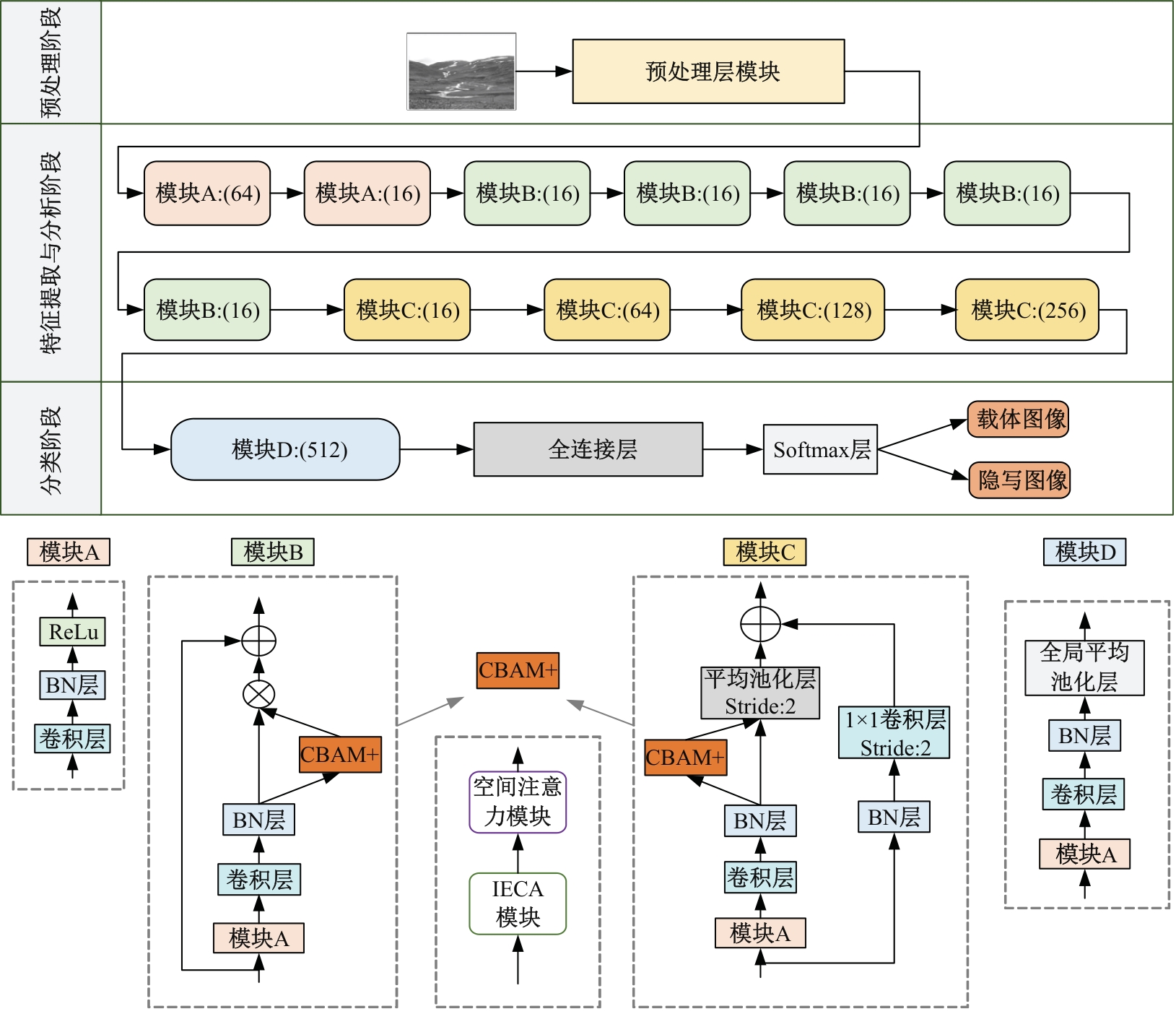
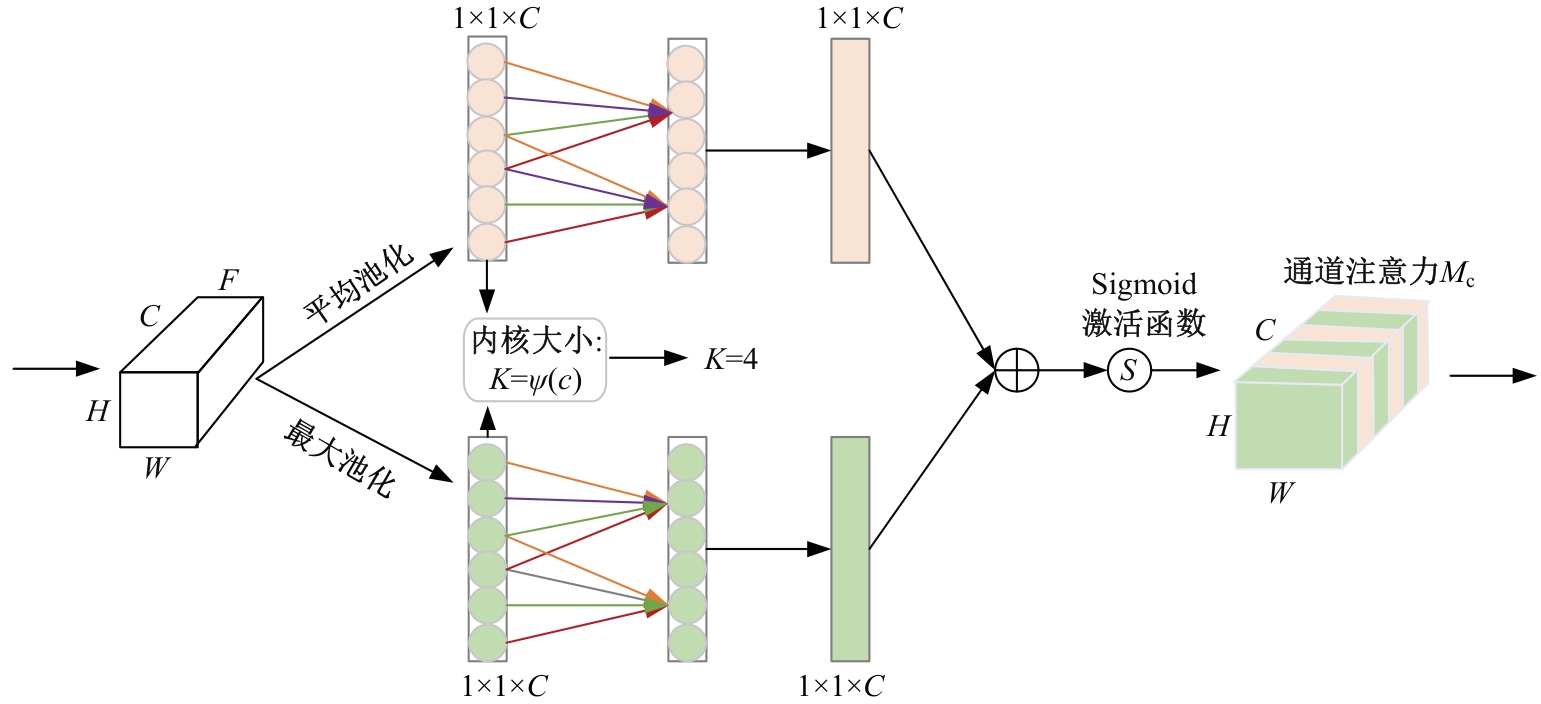
Spatial image steganography based on preprocessing layer enhancement and attention mechanism
Wei-wei LUO( ),Chang-long LIU,Qin LEI(
),Chang-long LIU,Qin LEI( )
)
- School of Electronic and Information Engineering,Lanzhou Jiaotong University,Lanzhou 730070,China
CLC Number:
- TP309
| [1] | Xiang S J, Luo X R. Reversible data hiding in encry pted image based on homomorphic public key crypt osystem[J]. Journal of Software, 2016, 27(6): 1592- 1601. |
| [2] | 陈君夫, 付章杰, 张卫明, 等. 基于深度学习的图像隐写分析综述[J]. 软件学报,2021, 32(2): 551-578. |
| Chen Jun-fu, Fu Zhang-jie, Zhang Wei-ming, et al. A review of image steganography based on deep learning [J]. Journal of Software, 2021, 32(2): 551-578. | |
| [3] | Fridrich J, Kodovsky J. Rich models for steganalysis of digital images[J]. IEEE Transactions on Information Forensics and Security, 2012, 7(3): 868-882. |
| [4] | Holub V, Fridrich J. Low-complexity features for JPEG steganalysis using undecimated DCT[J]. IEEE Transactions on Information Forensics and Security, 2014, 10(2): 219-228. |
| [5] | Holub V, Fridrich J. Phase-aware projection model for steganalysis of JPEG images[C]∥Media Watermarking, Security, and Forensics,Philadelphia, USA,2015:75-84. |
| [6] | Khan A, Sohail A, Zahoora U,et al. A survey of the recent architectures of deep convolutional neural networks[J]. Artificial Intelligence Review, 2020, 53: 5455-5516. |
| [7] | Chollet F. Xception: deep learning with depthwise separable convolutions[C]∥Proc IEEE Conf Comput Vis Pattern Recognit (CVPR),Honolulu, USA, 2017: 1800-1807. |
| [8] | He K, Zhang X, Ren S, et al. Deep residual learning for image recognition[C]∥Proc IEEE Conf Comput Vis Pattern Recognit (CVPR), Las Vegas,USA, 2016: 770-778. |
| [9] | Szegedy C, Ioffe S, Vanhoucke V, et al. Inception-v4, inception-ResNet and he impact of residual connections on learning[C]∥AAAI Conf Artif Intell,San Francisco,USA, 2017: 4278-4284. |
| [10] | Qian Y, Dong J, Wang W, et al. Learning and transferring representations for image steganalysis using convolutional neural network[C]∥IEEE International Conference on Image Processing(ICIP), Phoenix, USA, 2016: 2752-2756. |
| [11] | Jian Y, Ni J, Yang Y.Deep learning hierarchical representations for image steganalysis[J].IEEE Trans. Inf Forensic Secur,2017,12 (11): 2545-2557. |
| [12] | Zhang X B, Zhang X P, Feng G. Image steganalysis network based on dual-attention mechanism[J]. IEEE Signal Processing Letters, 2023, 30: 1287-1291. |
| [13] | Qian Y, Dong J, Wang W, et al. Deep learning for steganalysis via convolutional neural networks[C]∥Media Watermarking, Security, and Forensics, San Francisco, USA, 2015: 171-180. |
| [14] | Xu G, Wu H Z, Shi Y Q. Structural design of convolutional neural networks for steganalysis[J]. IEEE Signal Processing Letters, 2016, 23(5): 708-712. |
| [15] | Ye J, Ni J, Yi Y. Deep learning hierarchical representations for image steganalysis[J]. IEEE Transactions on Information Forensics and Security, 2017, 12(11): 2545-2557. |
| [16] | Zhang R, Zhu F, Liu J, et al. Depth-wise separable convolutions and multi-level pooling for an efficient spatial CNN-based steganalysis[J]. IEEE Transactions on Information Forensics and Security, 2019, 15: 1138-1150. |
| [17] | Han X, Zhang T. Spatial steganalysis based on non-local block and multi-channel convolutional networks[J]. IEEE Access, 2022, 10: 87241-87253. |
| [18] | Li B, Li Z, Zhou S, et al. New steganalytic features for spatial image steganography based on derivative filters and threshold LBP operator[J]. IEEE Transactions on Information Forensics and Security, 2017, 13(5): 1242-1257. |
| [19] | 史晓裕, 李斌, 谭舜泉. 深度学习空域隐写分析的预处理层[J]. 应用科学学报,2018, 36(2): 309-320. |
| Shi Xiao-yu, Li Bin, Tan Shun-quan. Preprocessing layer for deep learning spatial steganography [J]. Chinese Journal of Applied Sciences, 2018, 36(2): 309-320. | |
| [20] | Li B, Wei W, Ferreira A, et al. ReST-Net: diverse activation modules and parallel subnets-based CNN for spatial image steganalysis[J]. IEEE Signal Processing Letters, 2018, 25(5): 650-654. |
| [21] | Hu J, Shen L, Sun G. Squeeze-and-excitation networks[C]∥Proceedings of the IEEE Conference on Computer Vision and Pattern Recognition, Salt Lake City, USA, 2018: 7132-7141. |
| [22] | Woo S, Park J, Lee J Y, et al. Cbam: convolutional block attention module[C]∥Proceedings of the European Conference on Computer Vision (ECCV), Munich, Germany, 2018: 3-19. |
| [23] | Wang Q, Wu B, Zhu P, et al. ECA-Net: efficient channel attention for deep convolutional neural networks[C]∥Proceedings of the IEEE/CVF Conference on Computer Vision and Pattern Recognition, Seattle, USA, 2020:11531-11539. |
| [24] | Bas P, Filler T, Pevný T. Break our steganographic system: the ins and outs of organizing BOSS[C]∥International Workshop on Information Hiding, Prague, Czech Republic, 2011: 59-70. |
| [25] | Bas P, Furon T. BOWS-2. [DB/OL]. [2024-04-12]. . |
| [26] | He T, Zhang Z, Zhang H, et al. Bag of tricks for image classification with convolutional neural networks[C]∥Proceedings of the IEEE/CVF Conference on Computer Vision and Pattern Recognition, Long Beach, USA, 2019: 558-567. |
| [27] | Boroumand M, Chen M, Fridrich J. Deep residual network for steganalysis of digital images[J]. IEEE Transactions on Information Forensics and Security, 2018, 14(5): 1181-1193. |
| [1] | Jing TIAN,She-qiang MA,Xian-min SONG,Dan ZHAO,Fa-cheng CHEN. Adaptive convolutional network for traffic state estimation under sparse data [J]. Journal of Jilin University(Engineering and Technology Edition), 2025, 55(8): 2579-2587. |
| [2] | Hong XIAO,Xian-de LIU. Real-time acquisition and dynamic analysis of learning state based on hybrid intelligence [J]. Journal of Jilin University(Engineering and Technology Edition), 2025, 55(7): 2402-2408. |
| [3] | Zhi-gang FENG,Shou-qi WANG,Ming-yue YU. Rolling bearing fault diagnosis based on variational mode extraction and lightweight network [J]. Journal of Jilin University(Engineering and Technology Edition), 2025, 55(6): 1883-1891. |
| [4] | Rui-shan DU,Zi-shan WANG. Multi perspective facial expression recognition algorithm based on spatiotemporal attention [J]. Journal of Jilin University(Engineering and Technology Edition), 2025, 55(6): 2097-2102. |
| [5] | Hao WANG,Bin ZHAO,Guo-hua LIU. Temporal and motion enhancement for video action recognition [J]. Journal of Jilin University(Engineering and Technology Edition), 2025, 55(1): 339-346. |
| [6] | Sheng-jie ZHU,Xuan WANG,Fang XU,Jia-qi PENG,Yuan-chao WANG. Multi-scale normalized detection method for airborne wide-area remote sensing images [J]. Journal of Jilin University(Engineering and Technology Edition), 2024, 54(8): 2329-2337. |
| [7] | Xin-gang GUO,Chao CHENG,Zi-qi SHEN. Face expression recognition based on attention mechanism of convolution network [J]. Journal of Jilin University(Engineering and Technology Edition), 2024, 54(8): 2319-2328. |
| [8] | Ming-hui SUN,Hao XUE,Yu-bo JIN,Wei-dong QU,Gui-he QIN. Video saliency prediction with collective spatio-temporal attention [J]. Journal of Jilin University(Engineering and Technology Edition), 2024, 54(6): 1767-1776. |
| [9] | Xiao-hui WEI,Chen-yang WANG,Qi WU,Xin-yang ZHENG,Hong-mei YU,Heng-shan YUE. Systolic array-based CNN accelerator soft error approximate fault tolerance design [J]. Journal of Jilin University(Engineering and Technology Edition), 2024, 54(6): 1746-1755. |
| [10] | Chao XIA,Meng-jia WANG,Jian-yue Zhu,Zhi-gang YANG. Reduced-order modelling of a bluff body turbulent wake flow field using hierarchical convolutional neural network autoencoder [J]. Journal of Jilin University(Engineering and Technology Edition), 2024, 54(4): 874-882. |
| [11] | Li-ming LIANG,Long-song ZHOU,Jiang YIN,Xiao-qi SHENG. Fusion multi-scale Transformer skin lesion segmentation algorithm [J]. Journal of Jilin University(Engineering and Technology Edition), 2024, 54(4): 1086-1098. |
| [12] | Guo-jun YANG,Ya-hui QI,Xiu-ming SHI. Review of bridge crack detection based on digital image technology [J]. Journal of Jilin University(Engineering and Technology Edition), 2024, 54(2): 313-332. |
| [13] | Yu LU,Qian CHEN,Hai-bing YIN. Optimization algorithm for video coding based on convolutional neural networks [J]. Journal of Jilin University(Engineering and Technology Edition), 2024, 54(11): 3296-3301. |
| [14] | Xi-jun ZHANG,Ji-yang SHANG,Guang-jie YU,Jun HAO. Bearing fault diagnosis based on attention for multi-scale convolutional neural network [J]. Journal of Jilin University(Engineering and Technology Edition), 2024, 54(10): 3009-3017. |
| [15] | Xiang-jiu CHE,Huan XU,Ming-yang PAN,Quan-le LIU. Two-stage learning algorithm for biomedical named entity recognition [J]. Journal of Jilin University(Engineering and Technology Edition), 2023, 53(8): 2380-2387. |
|
||