吉林大学学报(工学版) ›› 2025, Vol. 55 ›› Issue (12): 4000-4009.doi: 10.13229/j.cnki.jdxbgxb.20240301
• 计算机科学与技术 • 上一篇
基于显著性检测的抗剪切攻击的图像数字水印方法
- 1.中国民航大学 计算机与人工智能学院,天津 300300
2.中国民航大学 安全科学与工程学院,天津 300300
3.中国民航大学 电子信息与自动化学院,天津 300300
Anti⁃cropping digital image watermarking based on saliency detection
Rui HUANG1( ),Ruo-xue YU1,Wei FAN1(
),Ruo-xue YU1,Wei FAN1( ),Yan XING2,Zi-yin CHEN3
),Yan XING2,Zi-yin CHEN3
- 1.School of Computer and Artificial Intelligence,Civil Aviation University of China,Tianjin 300300,China
2.School of Safety Science and Engineering,Civil Aviation University of China,Tianjin 300300,China
3.College of Electronic Information and Automation,Civil Aviation University of China,Tianjin 300300,China
摘要:
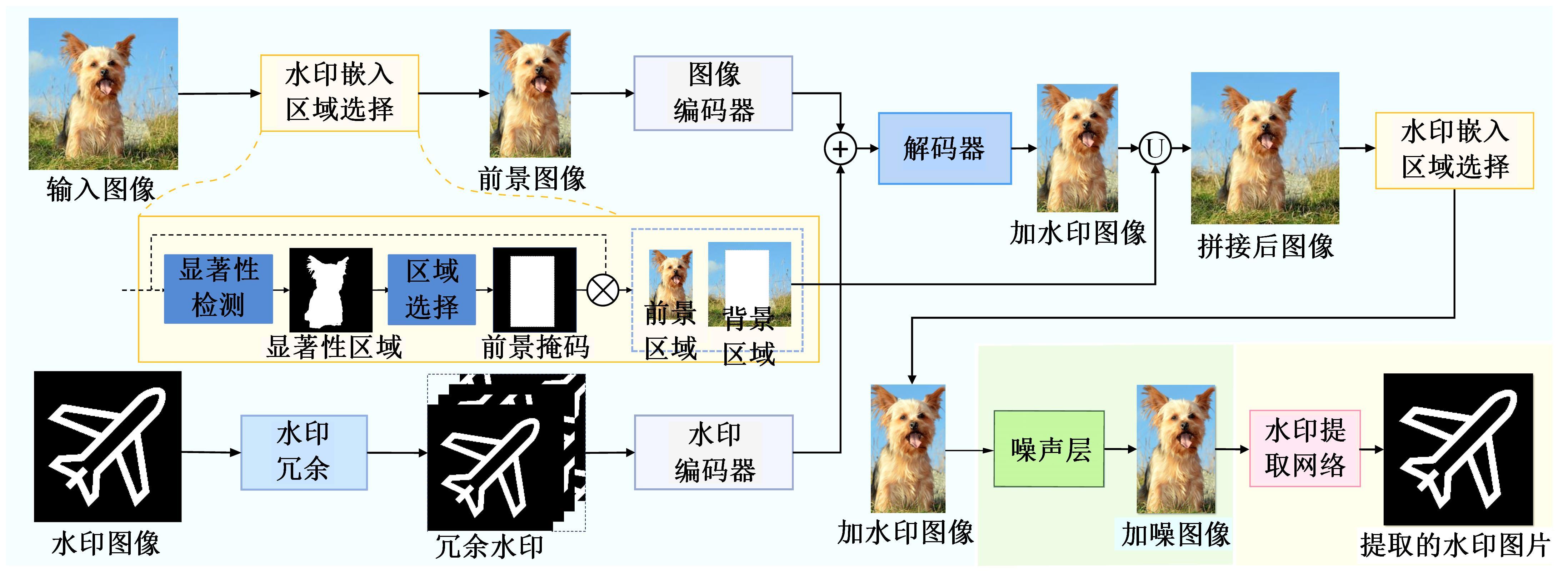
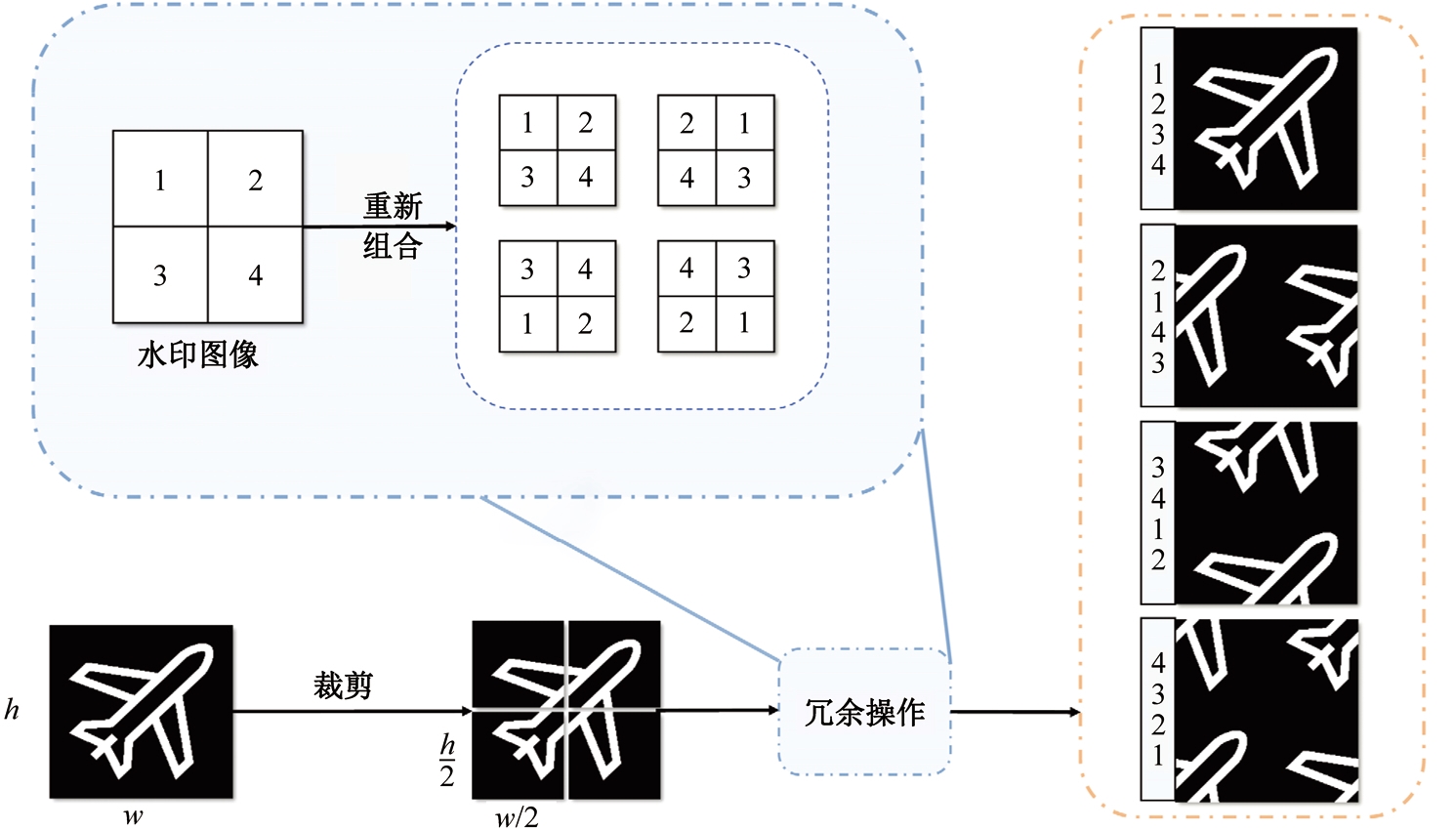
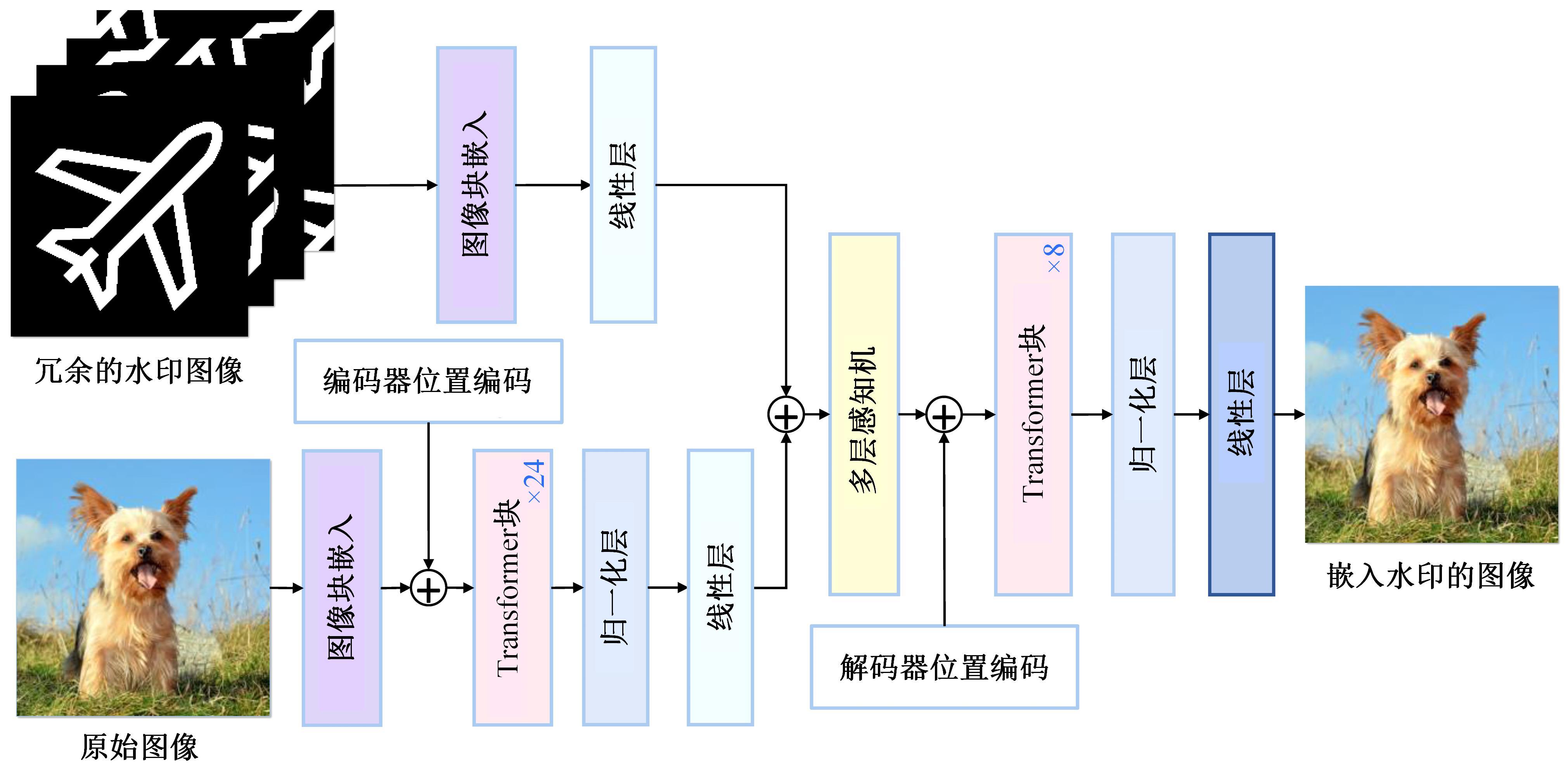
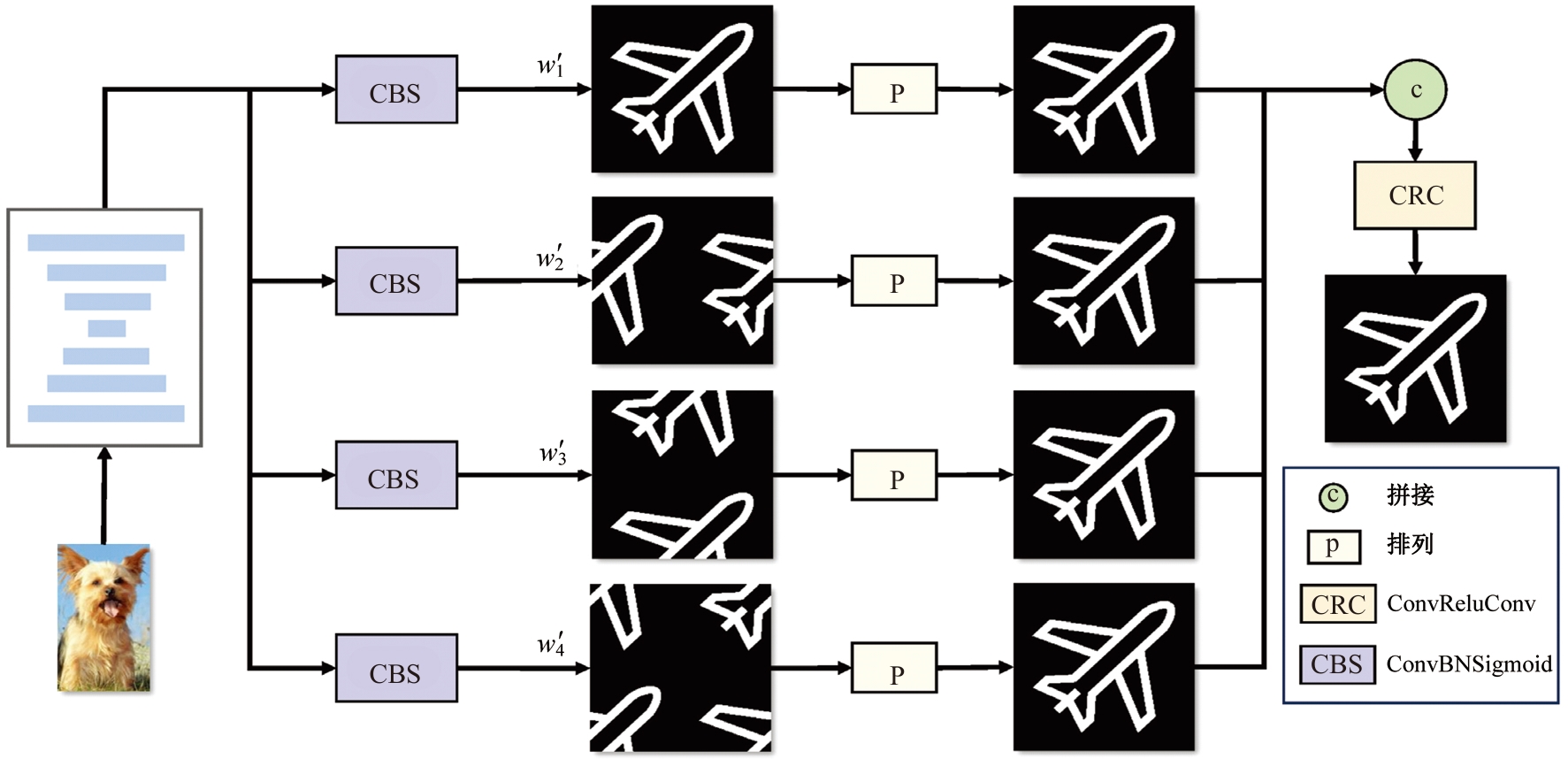
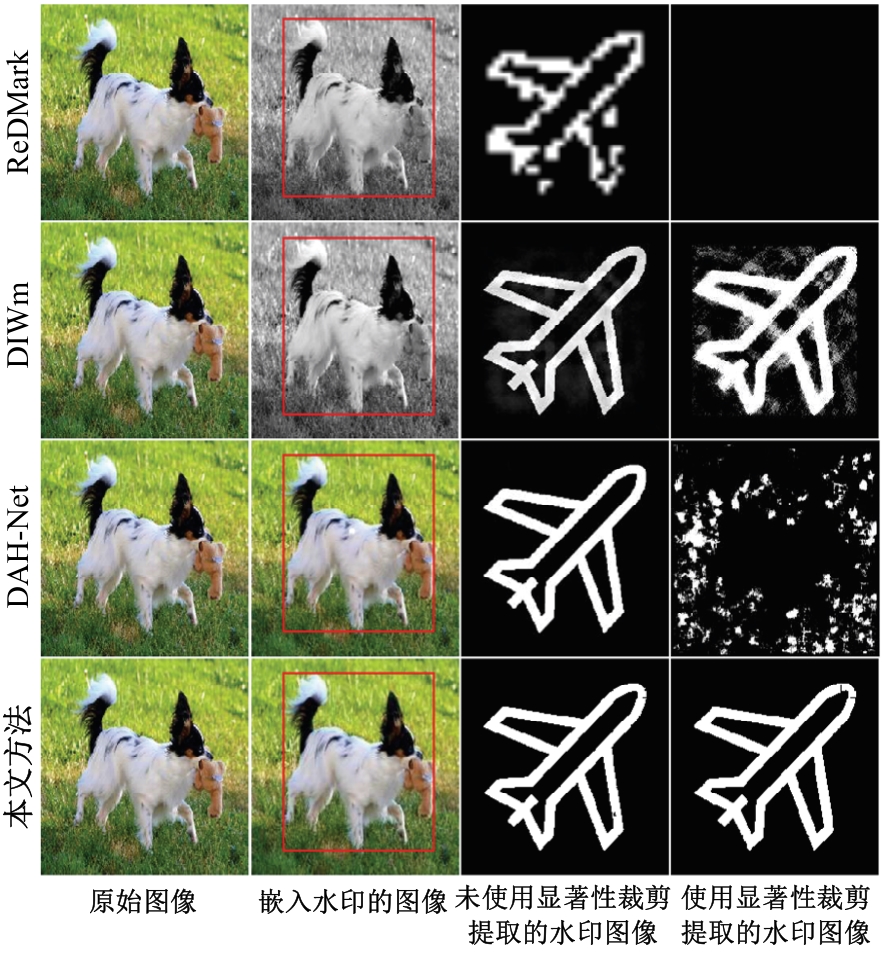
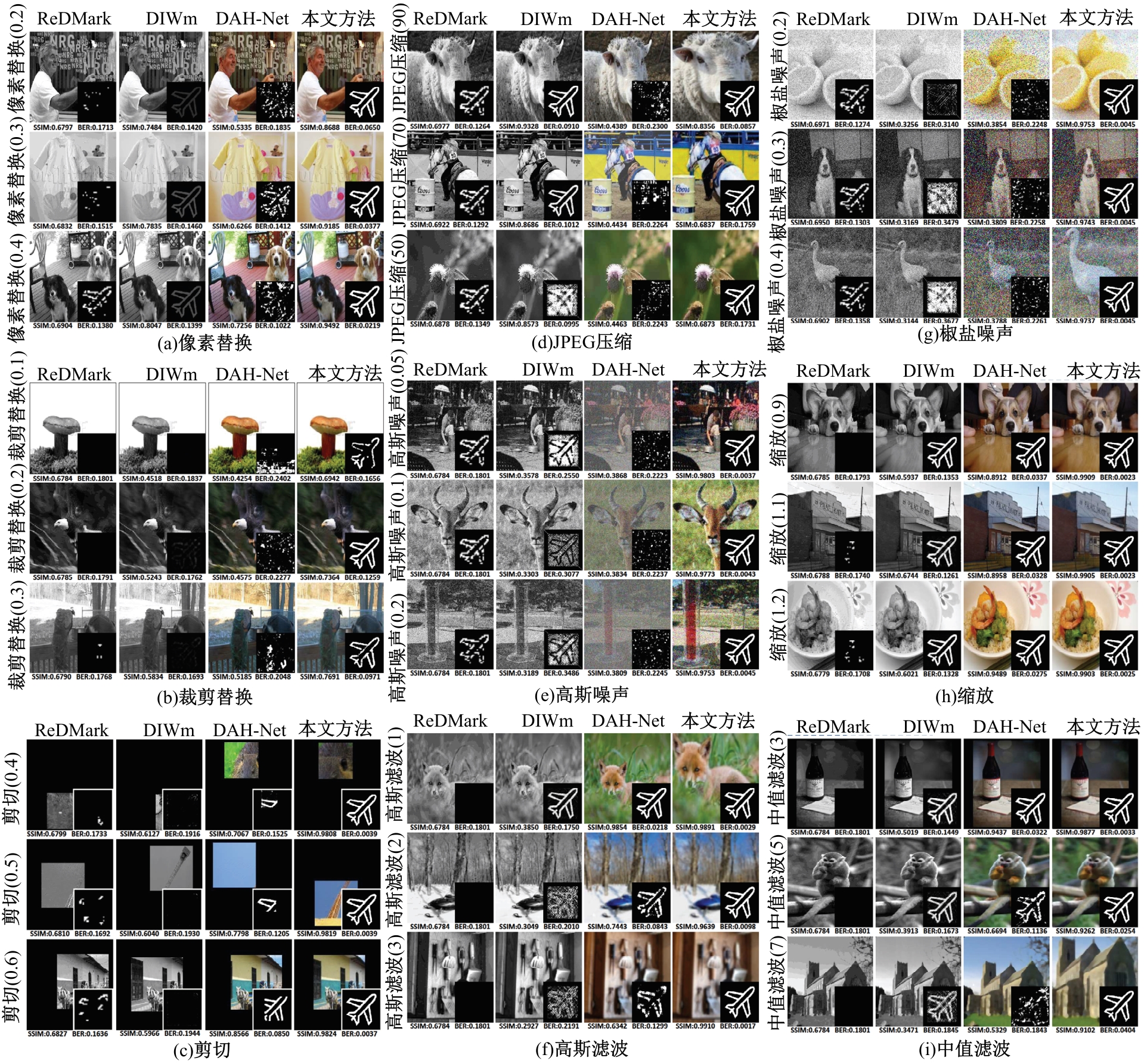
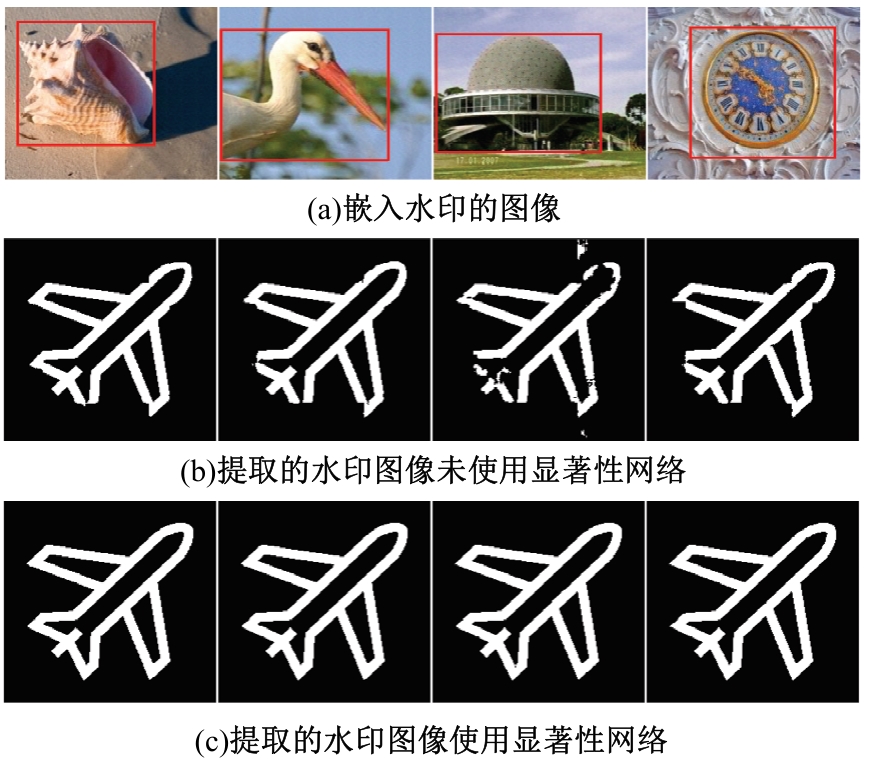
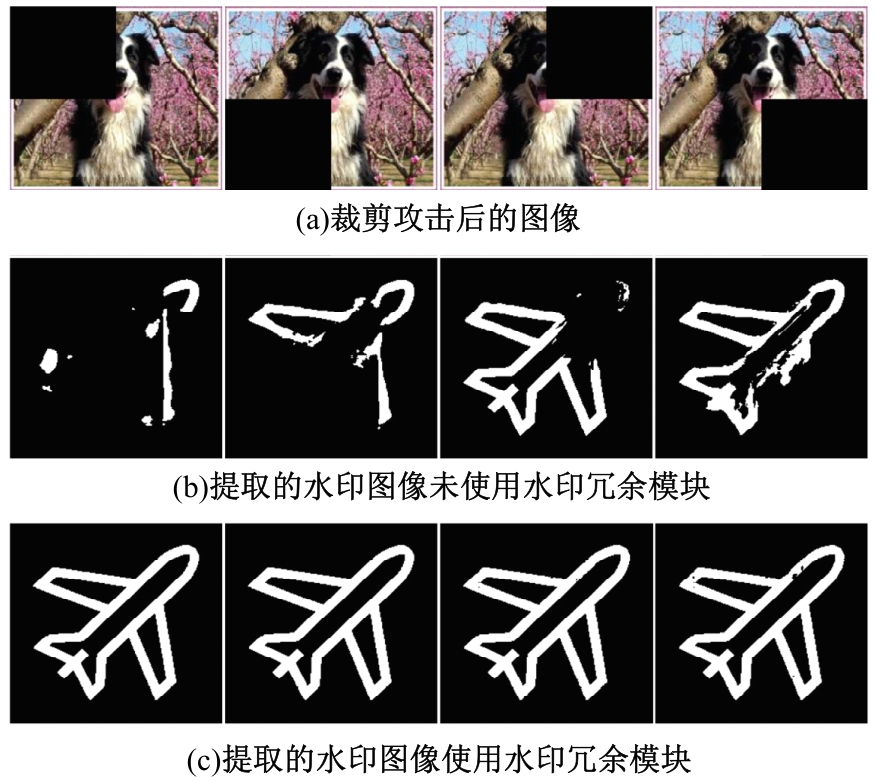
为了保证水印嵌入的区域在剪切时以较大的概率被保留,提出了基于显著性检测的抗剪切攻击的图像数字水印方法。首先,使用显著性检测网络确定嵌入区域;其次,使用Transformer网络将变换后的水印嵌入该区域中;再次,为了保证水印的鲁棒性,在提取水印之前,使用噪声层攻击嵌入水印的图像;最后,使用全卷积网络提取显著性区域中的水印。实验结果表明:在常见的9种攻击方法下,本文方法具有更好的鲁棒性;在基于显著性目标检测的剪切攻击时,本文方法依然可以准确地提取出水印。
中图分类号:
- TP309
| [1] | Van Schyndel R G, Tirkel A Z, Osborne C F. A digital watermark[C]∥Proceedings of 1st International Conference on Image Processing,Austin, USA, 1994: 86-90. |
| [2] | Ko H J, Huang C T, Horng G, et al. Robust and blind image watermarking in DCT domain using inter-block coefficient correlation[J]. Information Sciences, 2020, 517: 128-147. |
| [3] | Cedillo-Hernandez M, Cedillo-Hernandez A, Garcia-Ugalde F J. Improving dft-based image watermarking using particle swarm optimization algorithm[J]. Mathematics, 2021, 9(15): No. 1795. |
| [4] | Giri K J, Quadri S M K, Bashir R, et al. DWT based color image watermarking: a review[J]. Multimedia Tools and Applications, 2020, 79: 32881-32895. |
| [5] | Assini I, Badri A, Safi K, et al. A robust hybrid watermarking technique for securing medical image[J]. International Journal of Intelligent Engineering and Systems, 2018, 11(3): 169-176. |
| [6] | 李喜艳, 周夏冰, 刘征. 基于高容量强鲁棒的图像水印算法[J]. 吉林大学学报: 工学版, 2022, 52(1): 174-179. |
| Li Xi-yan, Zhou Xia-bing, Liu Zheng. High-capacity and robust image watermarking algorithm[J]. Journal of Jilin University (Engineering and Technology Edition), 2022, 52(1): 174-179. | |
| [7] | Hsu C S, Tu S F. Enhancing the robustness of image watermarking against cropping attacks with dual watermarks[J]. Multimedia Tools and Applications, 2020, 79(17/18): 11297-11323. |
| [8] | Liu J, Huang J, Luo Y, et al. An optimized image watermarking method based on HD and SVD in DWT domain[J]. IEEE Access, 2019, 7: 80849-80860. |
| [9] | Zhu J, Kaplan R, Johnson J, et al. Hidden: hiding data with deep networks[C]∥Proceedings of the European Conference on Computer Vision (ECCV),Munich, Germany, 2018: 657-672. |
| [10] | Lu J, Ni J, Su W, et al. Wavelet-based CNN for robust and high-capacity image watermarking[C]∥IEEE International Conference on Multimedia and Expo (ICME), Taipei, China, 2022: 1-6. |
| [11] | Liu Y, Guo M, Zhang J, et al. A novel two-stage separable deep learning framework for practical blind watermarking[C]∥Proceedings of the 27th ACM International Conference on Multimedia,Nice, France,2019: 1509-1517. |
| [12] | Zhang L, Lu Y, Li J, et al. Deep adaptive hiding network for image hiding using attentive frequency extraction and gradual depth extraction[J]. Neural Computing and Applications, 2023, 35(15): 10909-10927. |
| [13] | Marchesotti L, Cifarelli C, Csurka G. A framework for visual saliency detection with applications to image thumbnailing[C]∥IEEE 12th International Conference on Computer Vision, Kyoto, Japan, 2009: 2232-2239. |
| [14] | 刘洋, 毛克明. 基于自适应反馈机制的小差异化图像纹理特征信息数据检索[J]. 江苏大学学报: 自然科学版, 2025, 46(1): 73-81. |
| Liu yang, mao Ke-ming. Retrieval of texture feature information data for small differentiated images based on adaptive feedback mechanism[J]. Journal of Jiangsu University(Natural Science Edition), 2025, 46(1): 73-81. | |
| [15] | Tu Y, Niu L, Zhao W, et al. Image cropping with composition and saliency aware aesthetic score map[C]∥Proceedings of the AAAI Conference on Artificial Intelligence, New York, USA,2020: 12104-12111. |
| [16] | Thahab A T, Shahadi H I. Robust image watermarking against crop and rotation attacks for public communication networks[C]∥Third Scientific Conference of Electrical Engineering,Baghdad, Iraq, 2018: 105-110. |
| [17] | Jia Z, Fang H, Zhang W. Mbrs: enhancing robustness of dnn-based watermarking by mini-batch of real and simulated jpeg compression[C]∥Proceedings of the 29th ACM International Conference on Multimedia, Chengdu, China, 2021: 41-49. |
| [18] | Ding J, Cao Y, Shi C. CropDefender: deep watermark which is more convenient to train and more robust against cropping[J/OL].[2024-03-05]. |
| [19] | Tancik M, Mildenhall B, Ng R. Stegastamp: invisible hyperlinks in physical photographs[C]∥Proceedings of the IEEE/CVF Conference on Computer Vision and Pattern Recognition, Seattle, USA,2020: 2117-2126. |
| [20] | Ahmadi M, Norouzi A, Karimi N, et al. ReDMark: framework for residual diffusion watermarking based on deep networks[J]. Expert Systems with Applications, 2020, 146: No.113157. |
| [21] | Liu J J, Hou Q, Cheng M M, et al. A simple pooling-based design for real-time salient object detection[C]∥Proceedings of the IEEE/CVF Conference on Computer Vision and Pattern Recognition,Long Beach, USA, 2019: 3912-3921. |
| [22] | Deng J, Dong W, Socher R, et al. ImageNet: a large-scale hierarchical image database[C]∥IEEE Conference on Computer Vision and Pattern Recognition, Miami, USA, 2009: 248-255. |
| [1] | 艾青林,刘元宵,杨佳豪. 基于MFF-STDC网络的室外复杂环境小目标语义分割方法[J]. 吉林大学学报(工学版), 2025, 55(8): 2681-2692. |
| [2] | 张宇飞,王丽敏,赵建平,贾智尧,李明洋. 基于中心选择大逃杀优化算法的机器人逆运动学求解[J]. 吉林大学学报(工学版), 2025, 55(8): 2703-2710. |
| [3] | 于贵申,陈鑫,唐悦,赵春晖,牛艾佳,柴辉,那景新. 激光表面处理对铝-铝粘接接头剪切强度的影响[J]. 吉林大学学报(工学版), 2025, 55(8): 2555-2569. |
| [4] | 朴燕,康继元. RAUGAN:基于循环生成对抗网络的红外图像彩色化方法[J]. 吉林大学学报(工学版), 2025, 55(8): 2722-2731. |
| [5] | 刘琼昕,王甜甜,王亚男. 非支配排序粒子群遗传算法解决车辆位置路由问题[J]. 吉林大学学报(工学版), 2025, 55(7): 2464-2474. |
| [6] | 车翔玖,李良. 融合全局与局部细粒度特征的图相似度度量算法[J]. 吉林大学学报(工学版), 2025, 55(7): 2365-2371. |
| [7] | 李文辉,杨晨. 基于对比学习文本感知的小样本遥感图像分类[J]. 吉林大学学报(工学版), 2025, 55(7): 2393-2401. |
| [8] | 庄珊娜,王君帅,白晶,杜京瑾,王正友. 基于三维卷积与自注意力机制的视频行人重识别[J]. 吉林大学学报(工学版), 2025, 55(7): 2409-2417. |
| [9] | 赵宏伟,周伟民. 基于数据增强的半监督单目深度估计框架[J]. 吉林大学学报(工学版), 2025, 55(6): 2082-2088. |
| [10] | 王健,贾晨威. 面向智能网联车辆的轨迹预测模型[J]. 吉林大学学报(工学版), 2025, 55(6): 1963-1972. |
| [11] | 陈海鹏,张世博,吕颖达. 多尺度感知与边界引导的图像篡改检测方法[J]. 吉林大学学报(工学版), 2025, 55(6): 2114-2121. |
| [12] | 周丰丰,郭喆,范雨思. 面向不平衡多组学癌症数据的特征表征算法[J]. 吉林大学学报(工学版), 2025, 55(6): 2089-2096. |
| [13] | 车翔玖,孙雨鹏. 基于相似度随机游走聚合的图节点分类算法[J]. 吉林大学学报(工学版), 2025, 55(6): 2069-2075. |
| [14] | 刘萍萍,商文理,解小宇,杨晓康. 基于细粒度分析的不均衡图像分类算法[J]. 吉林大学学报(工学版), 2025, 55(6): 2122-2130. |
| [15] | 王友卫,刘奥,凤丽洲. 基于知识蒸馏和评论时间的文本情感分类新方法[J]. 吉林大学学报(工学版), 2025, 55(5): 1664-1674. |
|
||