吉林大学学报(工学版) ›› 2025, Vol. 55 ›› Issue (7): 2455-2463.doi: 10.13229/j.cnki.jdxbgxb.20230919
• 通信与控制工程 • 上一篇
融合交互信誉度与RSSR的WSNs女巫攻击检测策略
滕志军1,2( ),于沥博2,李明哲2,苗润升2,王继红1,2
),于沥博2,李明哲2,苗润升2,王继红1,2
- 1.东北电力大学 现代电力系统仿真控制与绿色电能新技术教育部重点实验室,吉林省 吉林市 132012
2.东北电力大学 电气工程学院,吉林省 吉林市 132012
WSNs sybil attack detection strategy integrating interactive reputation and RSSR
Zhi-jun TENG1,2( ),Li-bo YU2,Ming-zhe LI2,Run-sheng MIAO2,Ji-hong WANG1,2
),Li-bo YU2,Ming-zhe LI2,Run-sheng MIAO2,Ji-hong WANG1,2
- 1.Key Laboratory of Modern Power System Simulation and Control & Renewable Energy Technology,Ministry of Education,Northeast Electric Power University,Jilin 132012,China
2.School of Electrical Engineering,Northeast Electric Power University,Jilin 132012,China
摘要:
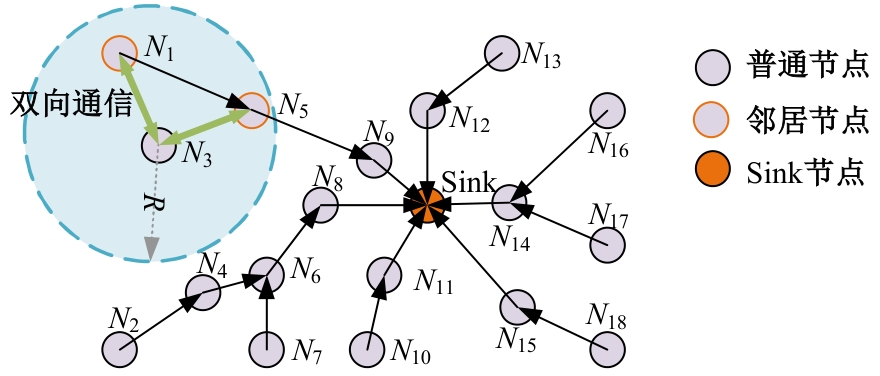
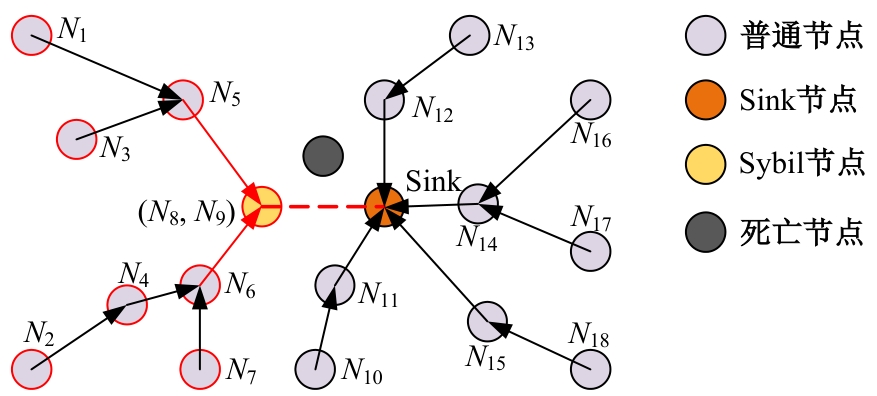
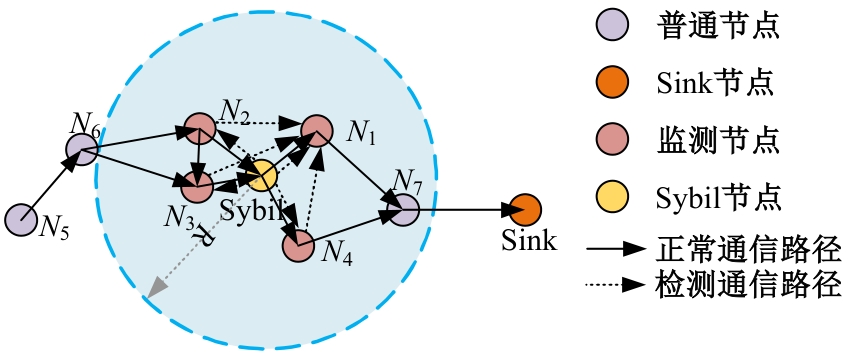
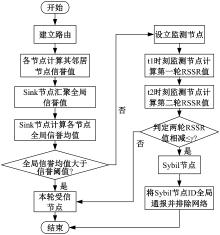
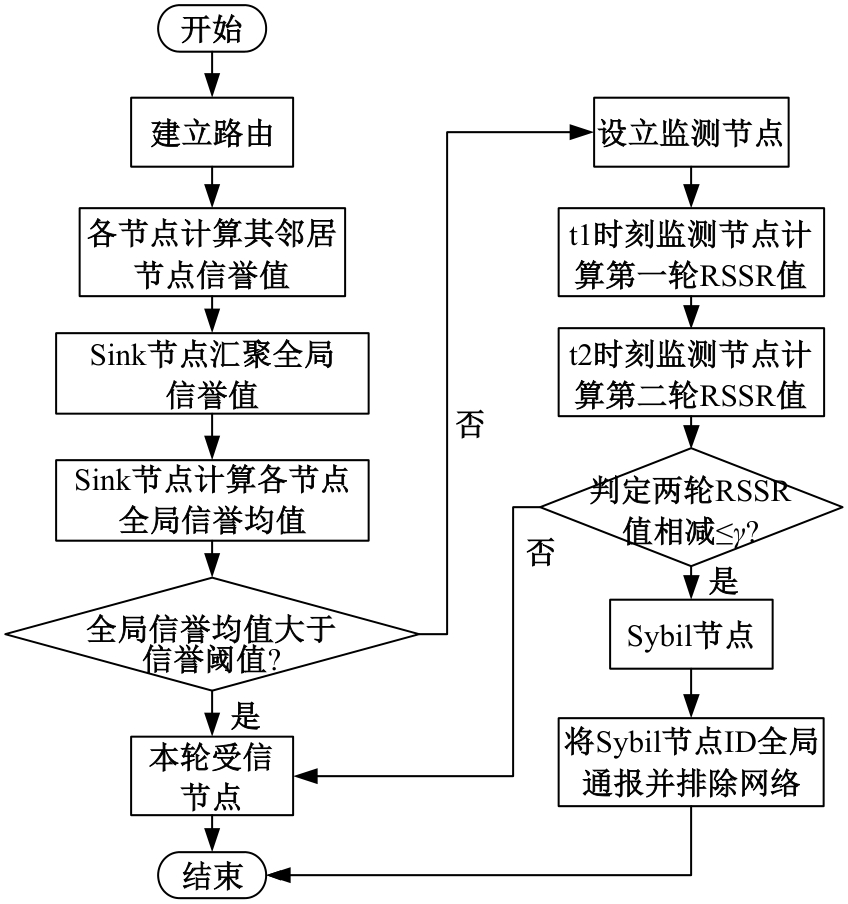
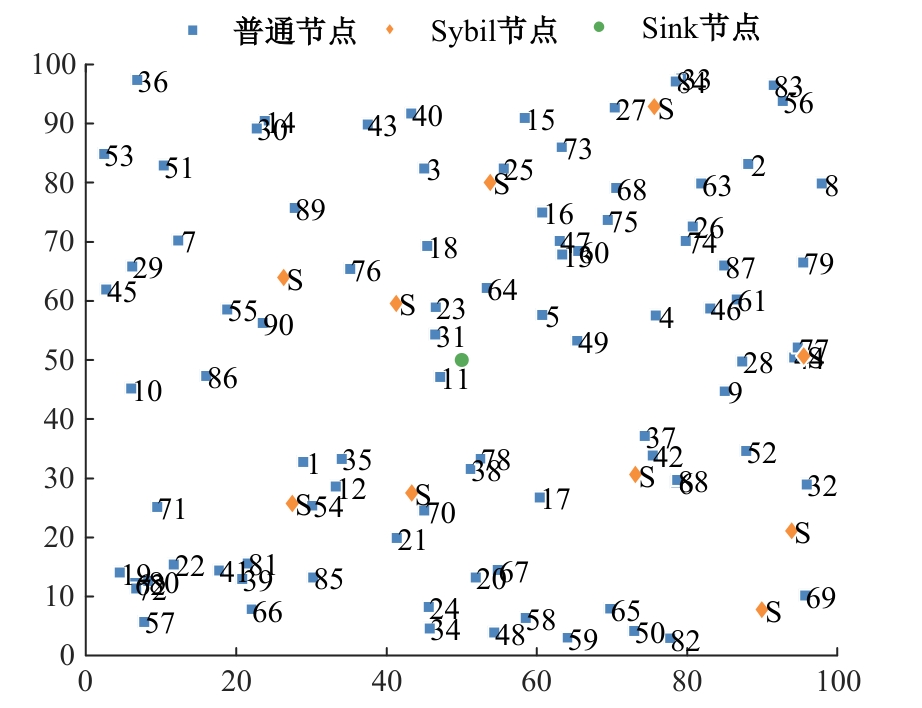
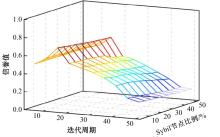
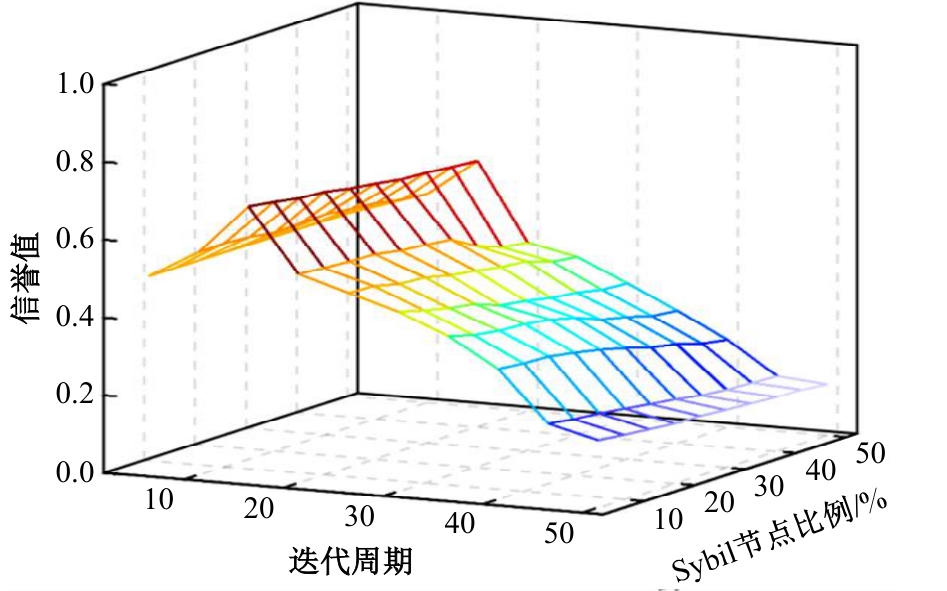
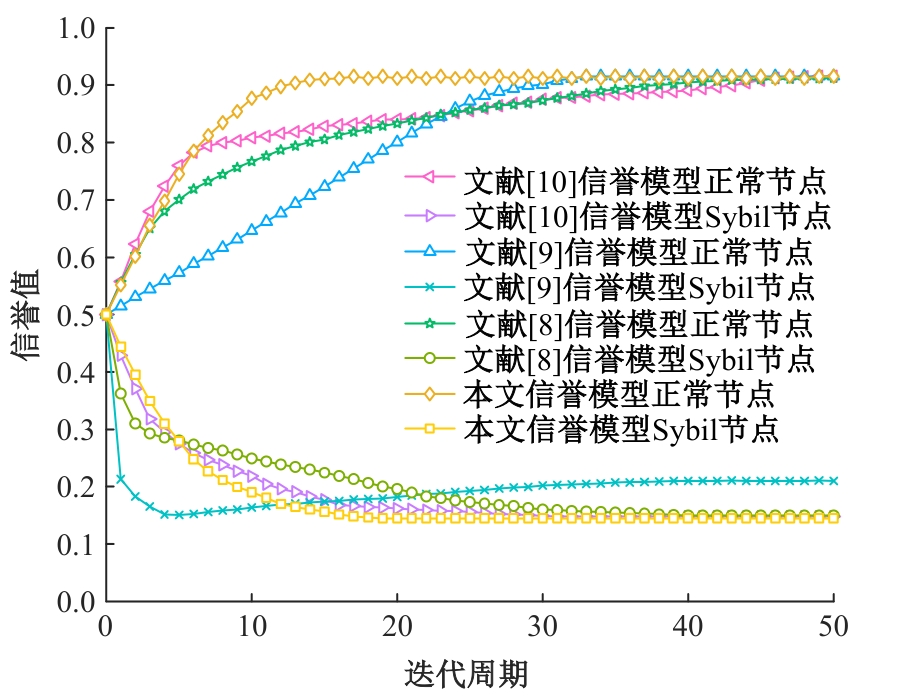
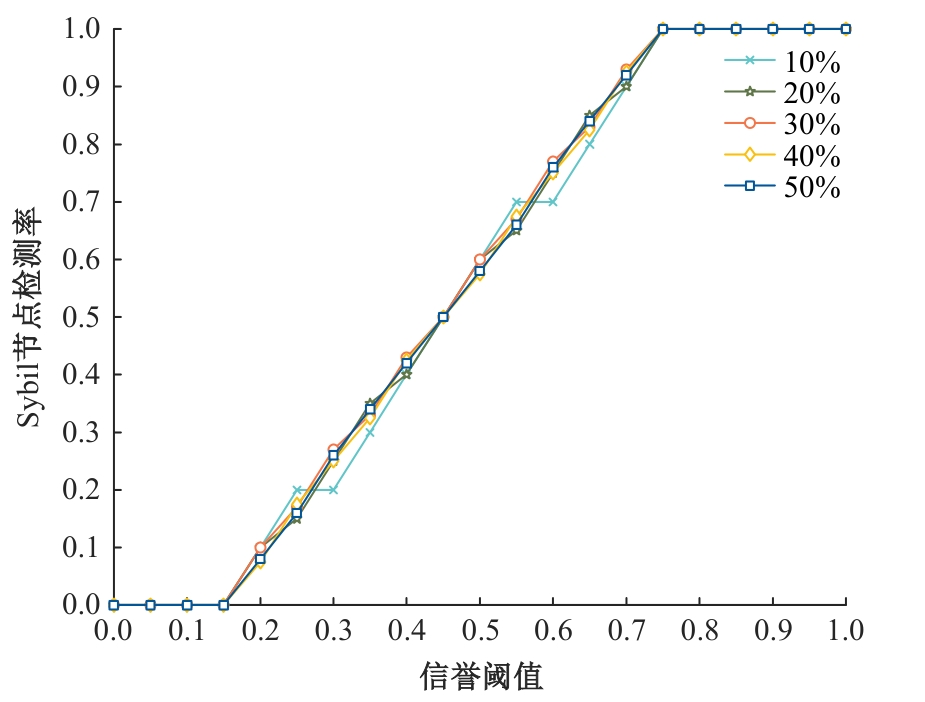
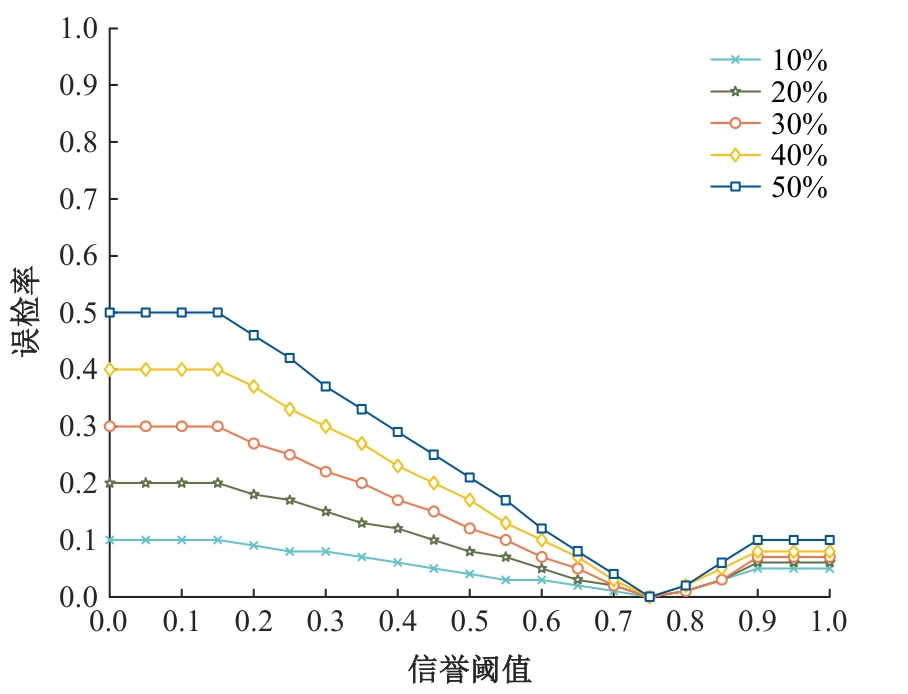
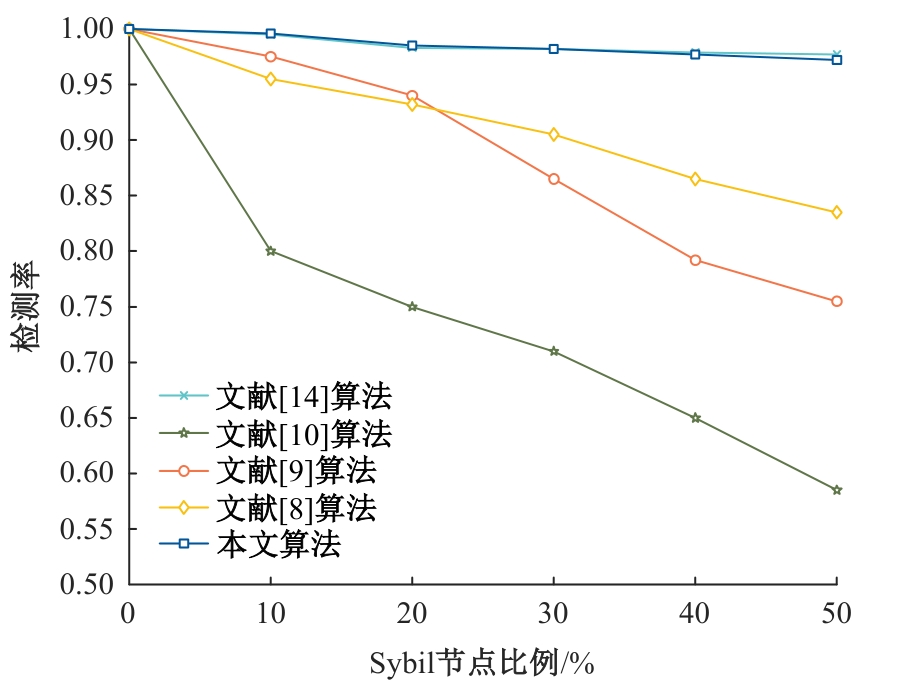
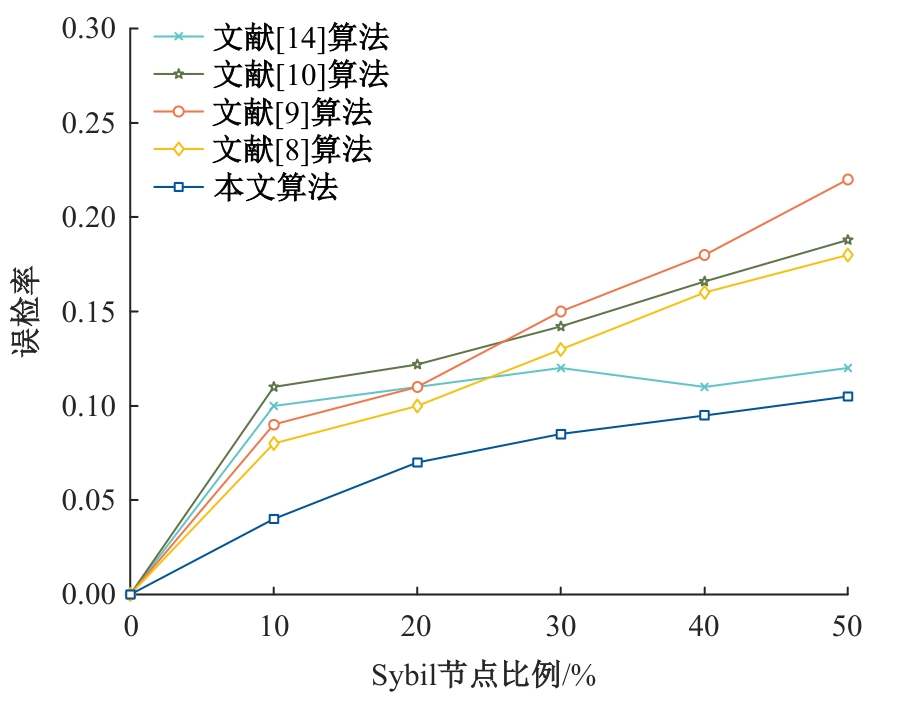
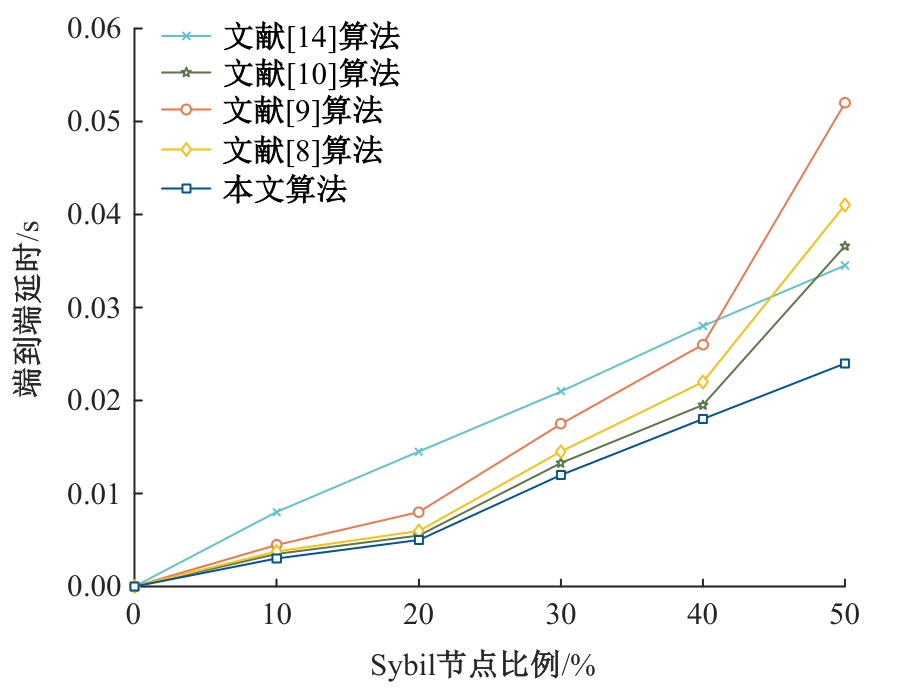
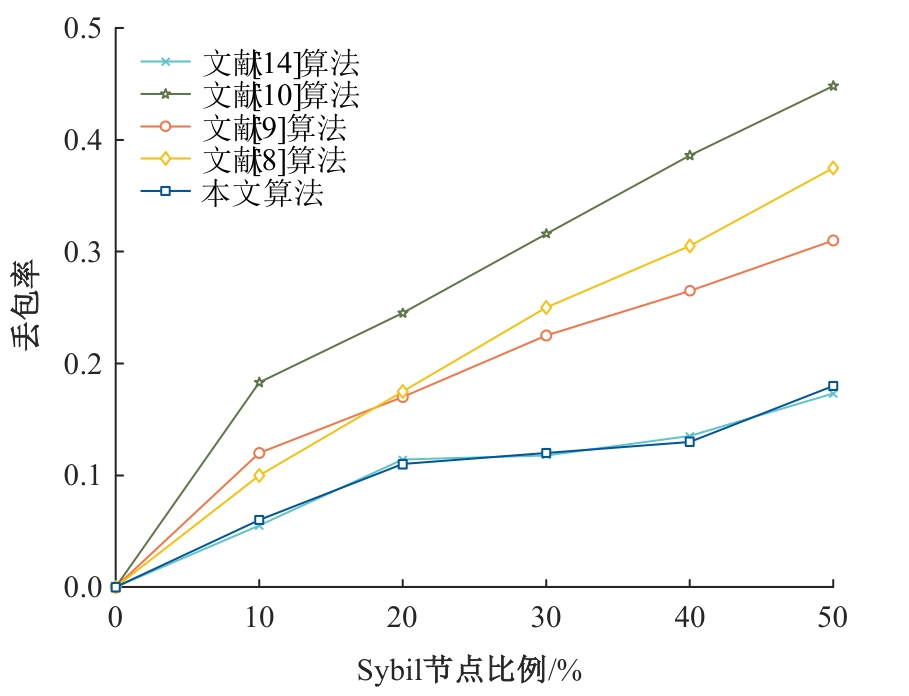
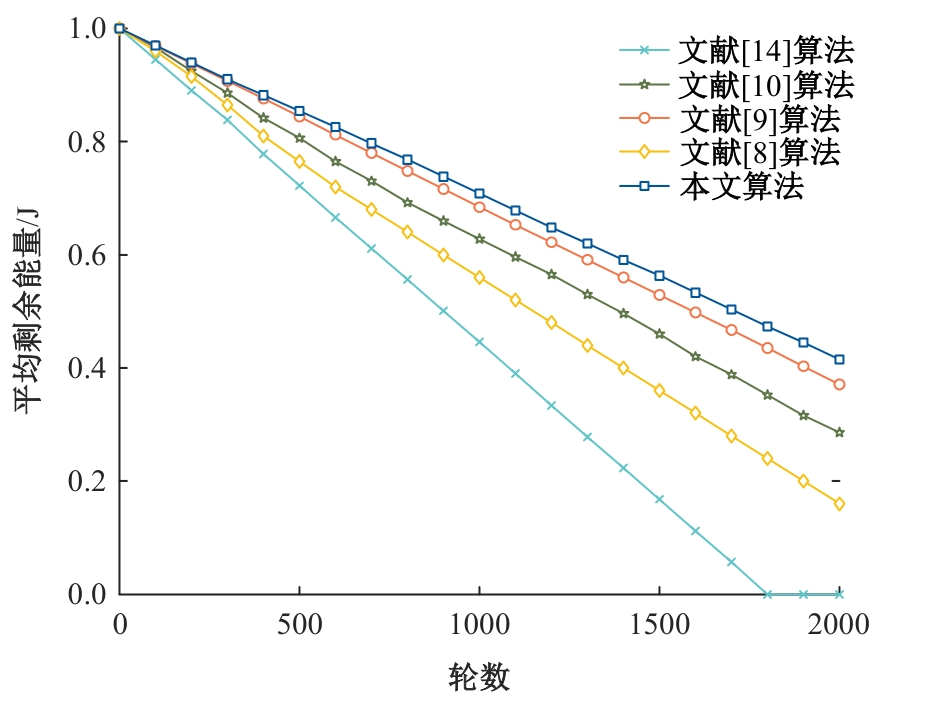
为抵御无线传感器网络中的女巫攻击,保护数据隐私,提出了一种融合交互信誉度与接收信号强度比(RSSR)的无线传感器网络女巫攻击检测策略(SD-IR&SR)。在计算节点交互信誉值时引入信誉维护函数和异常修正因子,以降低历史交互行为对信誉值的影响,建立全域信誉值矩阵计算各节点全域信誉均值,保障节点信誉值的公正;将全域信誉均值低于信誉阈值的节点列为不受信节点,设立监测节点,利用RSSR值比对法进行检测,以判定该节点是否为女巫节点。仿真结果表明,SD-IR&SR可以有效检测出网络中的女巫节点,即使在女巫节点占比50%的网络中依然能够保持较低的丢包率,保障数据完整、低延时传输,提高无线传感器网络的安全性。
中图分类号:
- TN92
| [1] | 金明, 丁蓉. 一种联合时域和空域残差的网络异常检测与节点定位方法[J]. 电子学报, 2023, 51(5): 1172-1178. |
| Jin Ming, Ding Rong. Detection and localization of outlier nodes in wireless sensor networks via Temporal and Spatial Residuals[J]. Acta Electronica Sinica, 2023, 51(5): 1172-1178. | |
| [2] | 王建元, 李南南. 基于一致性算法的直流微电网分布式储能系统能量控制策略[J]. 东北电力大学学报,2023, 43(2): 73-81. |
| Wang Jian-yuan, Li Nan-nan. Energy control strategy of DC miciogrid distributed energu storage system based on consensus algorithm[J]. Journal of Northeast Electric Power University, 2023, 43(2): 73-81. | |
| [3] | Wang H, Liu W, Xiong N N, et al. LIAA: a listen interval adaptive adjustment scheme for green communication in event-sparse IoT systems[J]. Information Sciences, 2022, 584: 235-268. |
| [4] | Amol V, Manu S. On the vulnerability of the mobile ad hoc network to transmission power controlled Sybil attack: adopting the mobility-based clustering[J]. Journal of King Saud University - Computer and Information Sciences, 2022, 34(9): 7025-7044. |
| [5] | 滕志军, 杜春秋, 孙汇阳, 等. 融合节点信誉度和路径跳数的WSNs虫洞攻击检测策略[J]. 哈尔滨工业大学学报, 2021, 53(8): 67-71, 131. |
| Teng Zhi-jun, Du Chun-qiu, Sun Hui-yang, et al. A wormhole attack detection strategy integrating node creditworthiness and path hops in WSNs[J]. Journal of Harbin Institute of Technology, 2021, 53(8): 67-71, 131. | |
| [6] | 国强, 崔玉强, 王勇. 无线传感器网络中基于动态簇的节点调度算法[J]. 吉林大学学报: 工学版, 2022, 52(6): 1466-1476. |
| Guo Qiang, Cui Yu-qiang, Wang Yong. Nodes scheduling algorithm based on dynamic cluster in wireless sensor network[J]. Journal of Jilin University (Engineering and Technology Edition), 2022, 52(6): 1466-1476. | |
| [7] | 邵春雨, 窦会光, 张海东, 等. 递归式变分模态分解在电力变压器声音信号降噪中的应用[J]. 东北电力大学学报, 2022, 42(5): 90-96. |
| Shao Chun-yu, Dou Hui-guang, Zhang Hai-dong, et al. Recursive variational modal decomposition for noise reduction of power transformer sound signals[J]. Journal of Northeast Electric Power University, 2022, 42(5): 90-96. | |
| [8] | Khan T, Singh K, Abdel-Basset M, et al. A novel and comprehensive trust estimation clustering based approach for large scale wireless sensor networks[J]. IEEE Access, 2019, 7: 58221-58240. |
| [9] | Anwar R W, Zainal A, Outay F, et al.BTEM: belief based trust evaluation mechanism for wireless sensor networks[J]. Future Generation Computer Systems, 2019, 96: 605-616. |
| [10] | Feng R, Han X, Liu Q, et al. A credible Bayesian-based trust management scheme for wireless sensor networks[J]. International Journal of Distributed Sensor Networks, 2015, 11(11): No.678926. |
| [11] | 叶正旺, 温涛, 刘振宁, 等. 基于信誉模型的WSNs安全数据融合算法[J]. 东北大学学报: 自然科学版, 2019, 40(6): 789-794. |
| Ye Zheng-wang, Wen Tao, Liu Zhen-ning, et al. An algorithm of trust-based secure data aggregation for wireless sensor networks[J]. Journal of Northeastern University (Natural Science), 2019, 40(6): 789-794. | |
| [12] | Urooj S, Lata S, Ahmad S, et al. Cryptographic data security for reliable wireless sensor network[J]. Alexandria Engineering Journal, 2023, 72: 37-50. |
| [13] | Dong S, Zhang X, Zhou W. A security localization algorithm based on DV-hop against Sybil attack in wireless sensor networks[J]. Journal of Electrical Engineering & Technology, 2020, 15: 919-926. |
| [14] | Jamshidi M, Zangeneh E, Esnaashari M, et al. A novel model of sybil attack in cluster-based wireless sensor networks and propose a distributed algorithm to defend it[J]. Wireless Personal Communications, 2019, 105: 145-173. |
| [15] | 邢小东. 基于动态WSN的抗合谋Sybil攻击检测方法[J]. 计算机仿真, 2021, 38(1): 416-420. |
| Xing Xiao-dong. Anti collusion sybil attack detection method based on dynamin wireless sensor network[J]. Computer Simulation, 2021, 38(1): 416-420. | |
| [16] | Hussain K, Xia Y, Onaizah A N, et al. Hybrid of WOA-ABC and proposed CNN for intrusion detection system in wireless sensor networks[J]. Optik, 2022, 271: 170145. |
| [17] | 李翠然, 王雪洁, 谢健骊, 等. 基于改进PSO的铁路监测线性无线传感器网络路由算法[J]. 通信学报, 2022, 43(5):155-165. |
| Li Cui-ran, Wang Xue-jie, Xie Jian-li, et al. Routing algorithm for railway monitoring linear WSN based on improved PSO[J]. Journal on Communications, 2022, 43(5): 155-165. |
| [1] | 李建坡,刘琨,朱伟华. 基于链路质量优化的无线传感器网络数据传输算法[J]. 吉林大学学报(工学版), 2024, 54(9): 2668-2675. |
| [2] | 特木尔朝鲁朝鲁,张亚萍. 基于卷积神经网络的无线传感器网络链路异常检测算法[J]. 吉林大学学报(工学版), 2024, 54(8): 2295-2300. |
| [3] | 王晓莹,陈小海. 嵌入式无线传感器网络多链路传输随机退避算法[J]. 吉林大学学报(工学版), 2024, 54(7): 2057-2062. |
| [4] | 段锦,姚安妮,王震,于林韬. 改进的麻雀搜索算法优化无线传感器网络覆盖[J]. 吉林大学学报(工学版), 2024, 54(3): 761-770. |
| [5] | 张楠,史建华,亿吉,王平. 基于加权质心定位的井下移动目标实时跟踪方法[J]. 吉林大学学报(工学版), 2023, 53(5): 1458-1464. |
| [6] | 王军,徐彦惠,李莉. 低能耗支持完整性验证的数据融合隐私保护方法[J]. 吉林大学学报(工学版), 2022, 52(7): 1657-1665. |
| [7] | 国强,崔玉强,王勇. 无线传感器网络中基于动态簇的节点调度算法[J]. 吉林大学学报(工学版), 2022, 52(6): 1466-1476. |
| [8] | 于斌斌,胡亮,迟令. 可抵抗内外部攻击的无线传感器网络数字签名方案[J]. 吉林大学学报(工学版), 2019, 49(5): 1676-1681. |
| [9] | 董颖, 崔梦瑶, 吴昊, 王雨后. 基于能量预测的分簇可充电无线传感器网络充电调度[J]. 吉林大学学报(工学版), 2018, 48(4): 1265-1273. |
| [10] | 刘洲洲, 彭寒. 基于节点可靠度的无线传感器网络拓扑控制算法[J]. 吉林大学学报(工学版), 2018, 48(2): 571-577. |
| [11] | 于斌斌, 武欣雨, 初剑峰, 胡亮. 基于群密钥协商的无线传感器网络签名协议[J]. 吉林大学学报(工学版), 2017, 47(3): 924-929. |
| [12] | 董颖, 周占颖, 苏真真, 徐洋, 钱志鸿. 基于路由信息的无线传感器网络跨层MAC协议[J]. 吉林大学学报(工学版), 2017, 47(2): 647-654. |
| [13] | 朱海洋, 张合, 马少杰. 增强型超声波周向旋转扫描节点参数优化[J]. 吉林大学学报(工学版), 2017, 47(1): 262-267. |
| [14] | 刘洲洲, 王福豹. 改进的离散混合蛙跳算法压缩感知信号重构及应用[J]. 吉林大学学报(工学版), 2016, 46(4): 1261-1268. |
| [15] | 张婧, 刘衍珩, 张晋东, 孙庚. 无线传感器网络簇半径自适应调整策略[J]. 吉林大学学报(工学版), 2016, 46(3): 876-883. |
|
||