吉林大学学报(工学版) ›› 2025, Vol. 55 ›› Issue (12): 3986-3999.doi: 10.13229/j.cnki.jdxbgxb.20240403
• 计算机科学与技术 • 上一篇
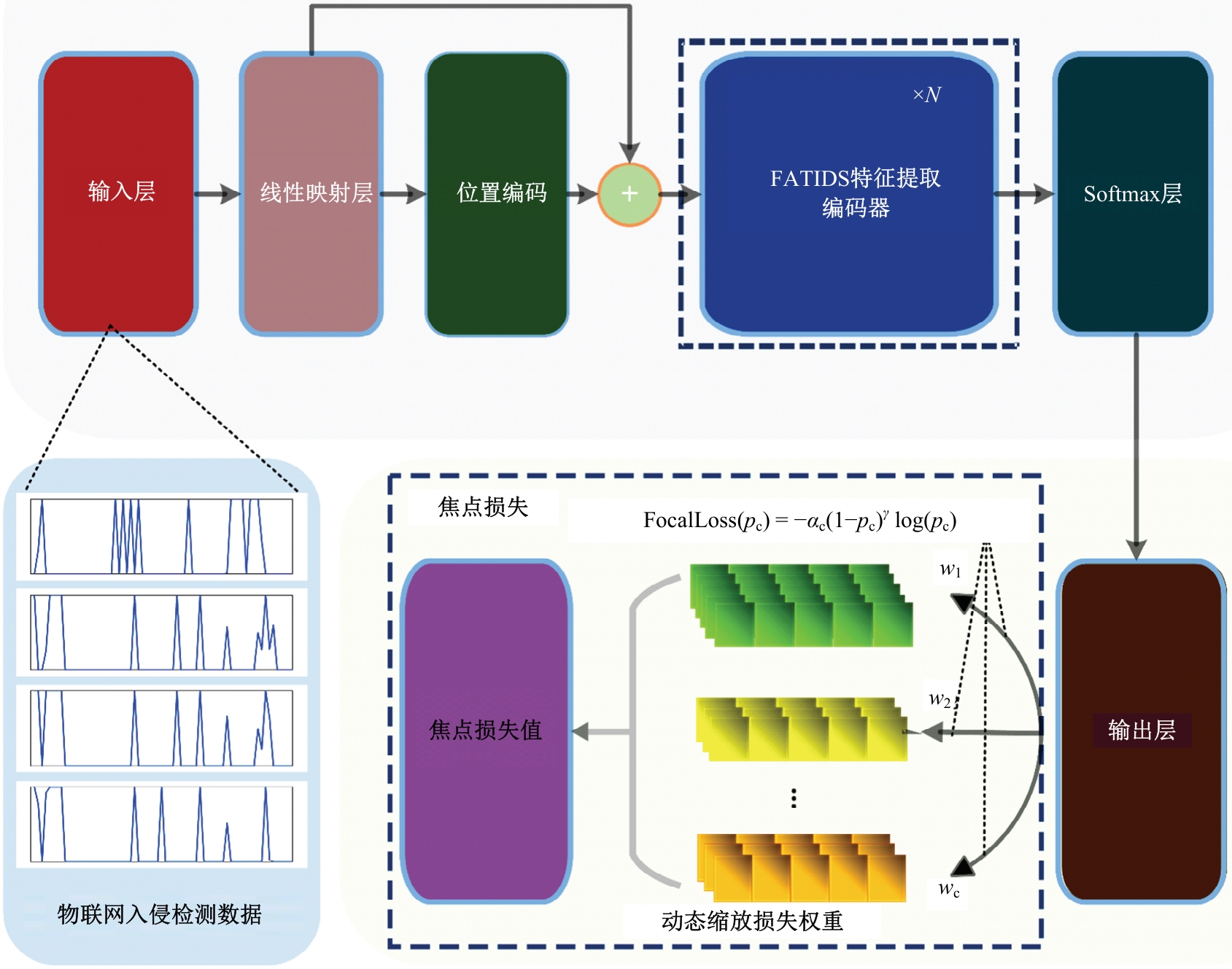
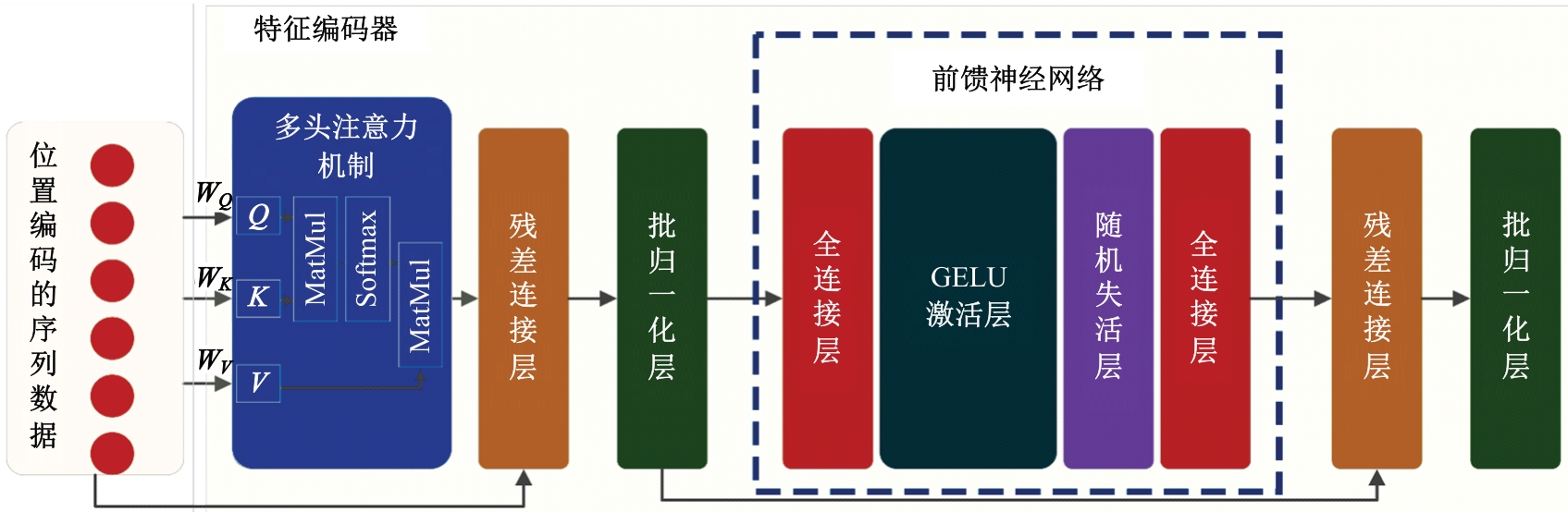
FATIDS:面向类不平衡样本的物联网入侵检测方法
- 空军工程大学 防空反导学院,西安 710051
FATIDS: an IoT intrusion detection method for class⁃imbalanced samples
Peng WANG( ),Ya-fei SONG,Xiao-dan WANG(
),Ya-fei SONG,Xiao-dan WANG( ),Yan-li LU,Qian XIANG
),Yan-li LU,Qian XIANG
- Air and Missile Defense College,Air Force Engineering University,Xi'an 710051,China
摘要:
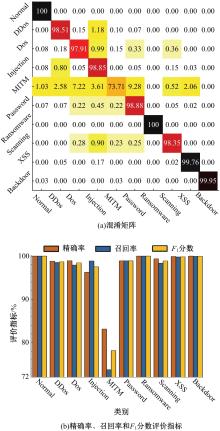
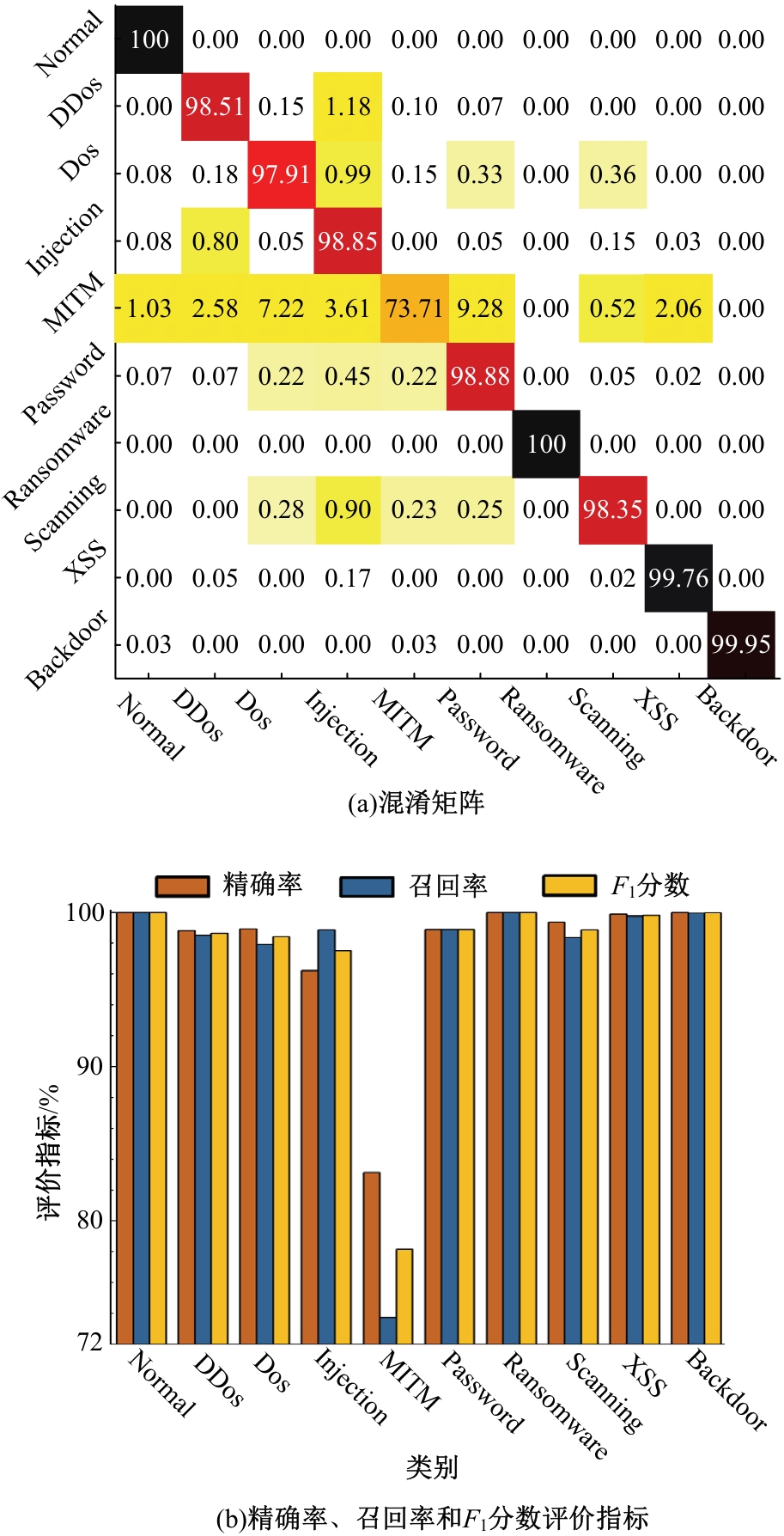
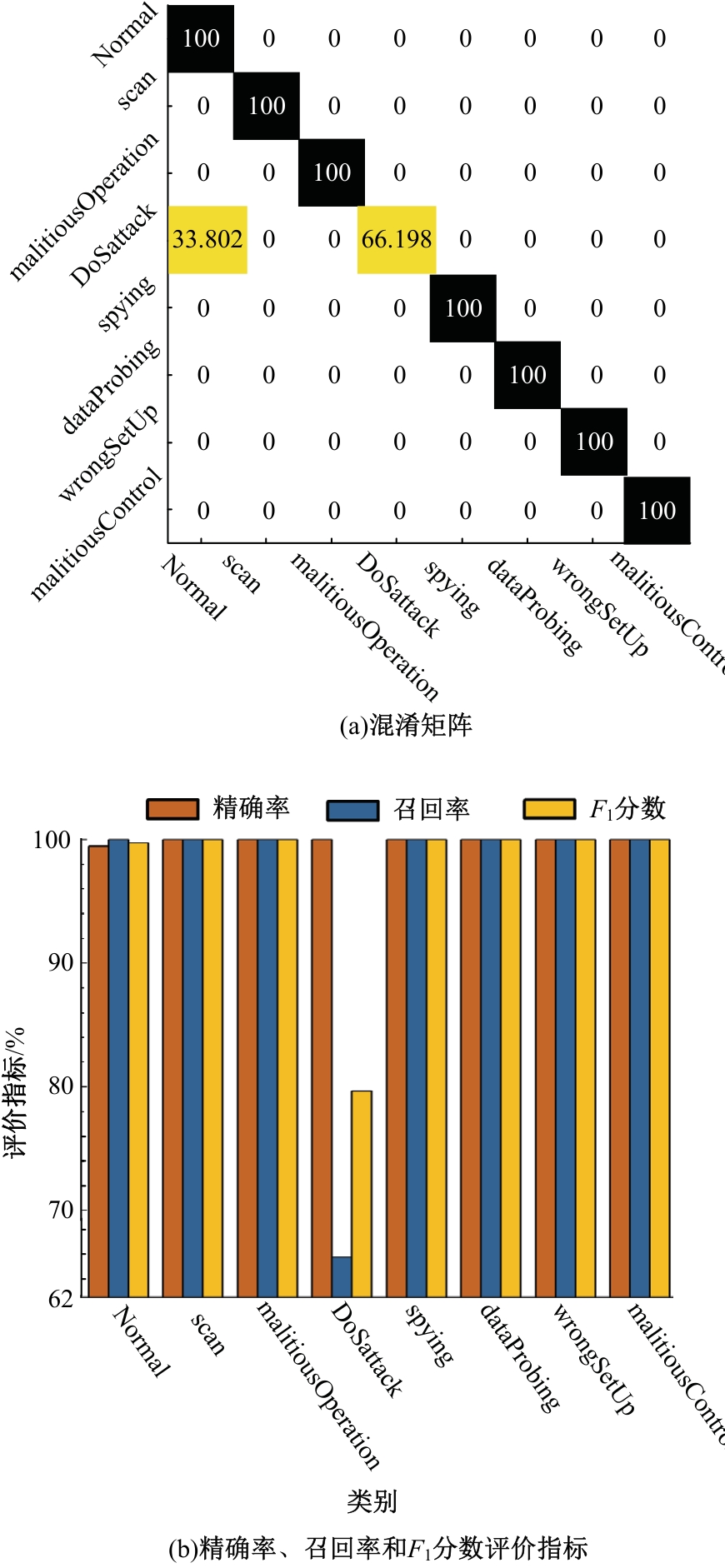
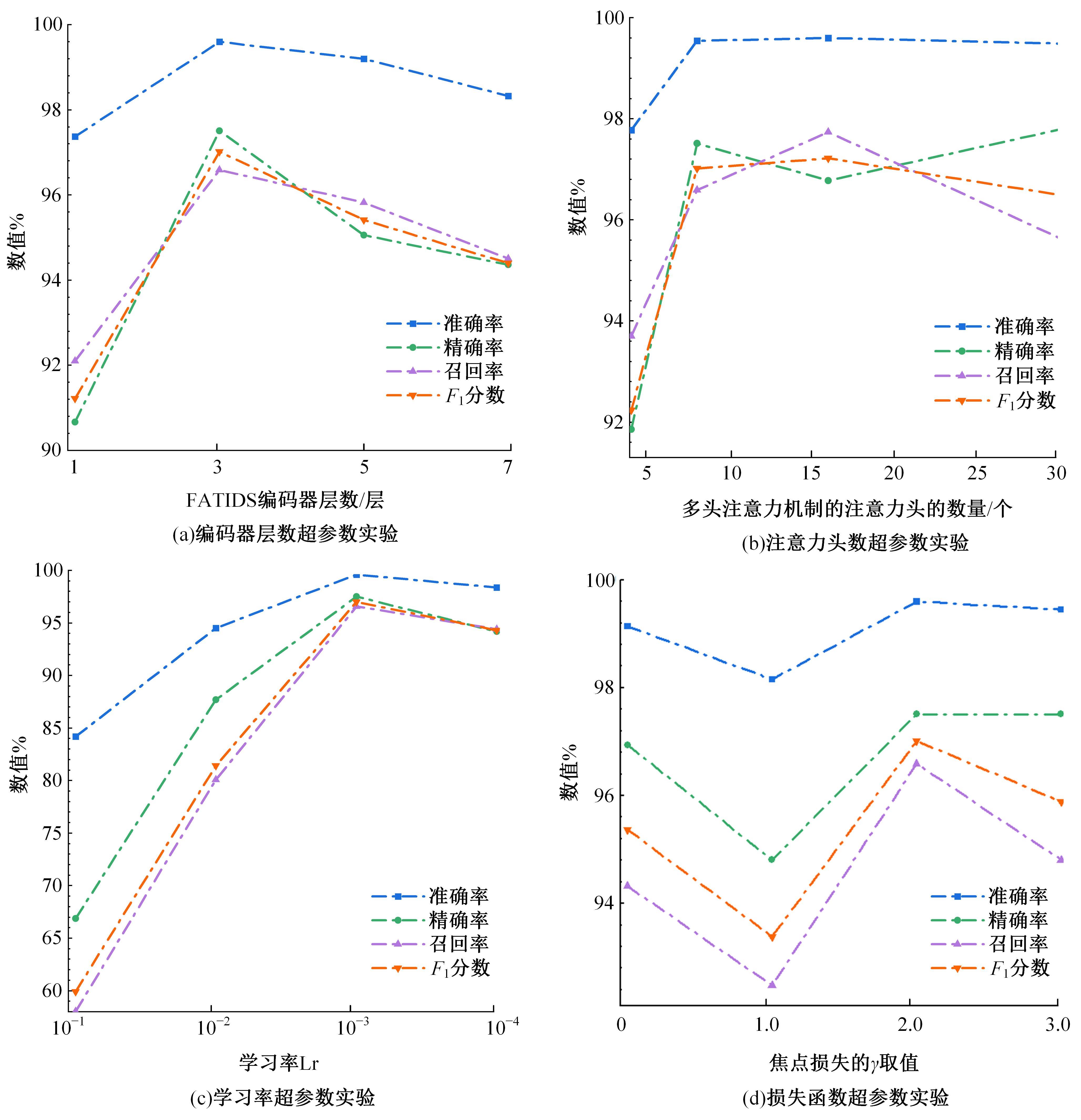
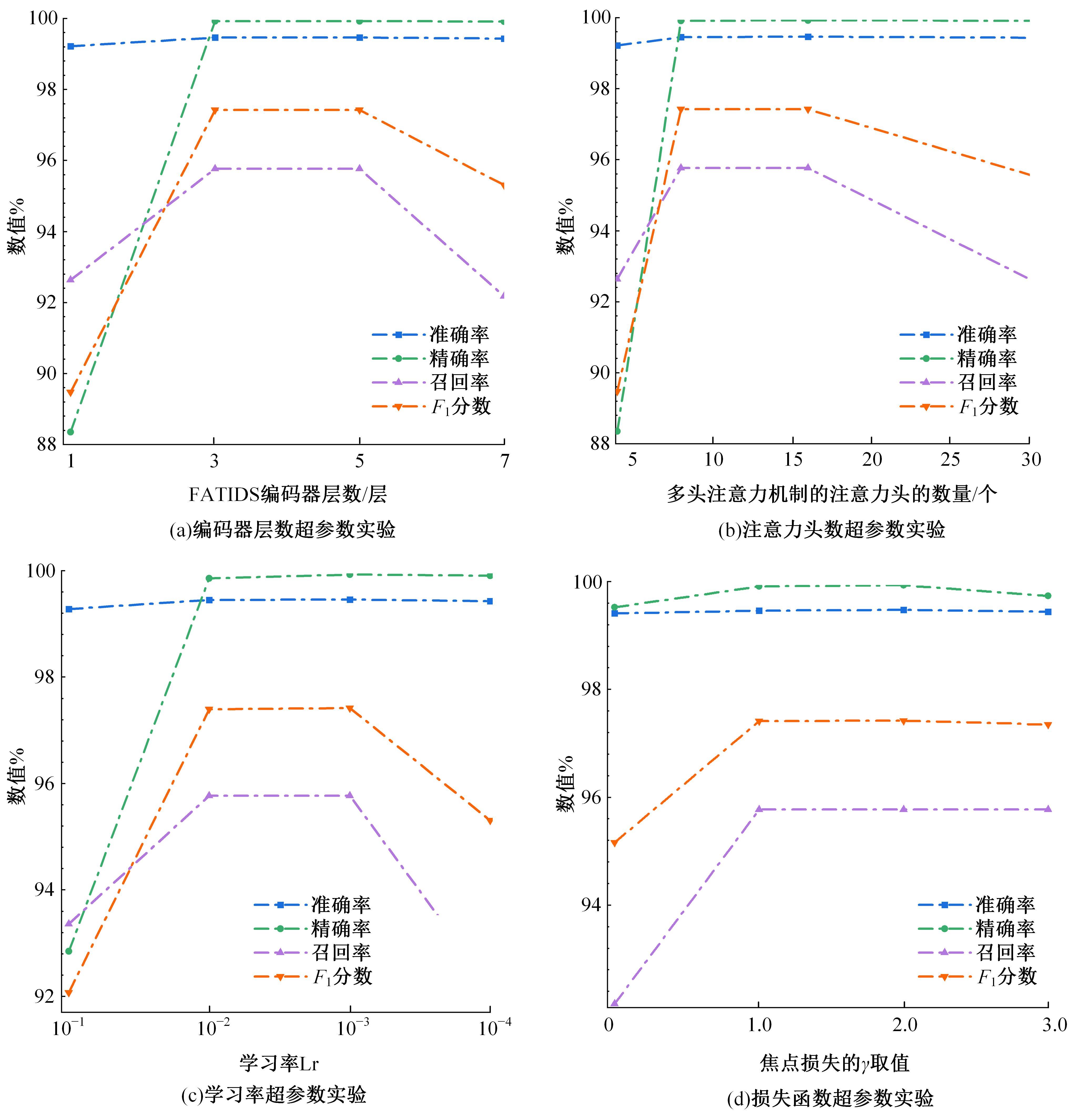
针对传统物联网入侵检测方法大多依赖复杂的特征预处理技术且对全局特征的建模能力不强,难以有效表示高维序列的抽象特征,从而对类不平衡数据的泛化性能较差的问题,提出了一种基于FATIDS的物联网入侵检测方法,通过自注意力机制实现了端到端的特征选择和特征提取,动态调整对序列特征的注意力权值,提高了针对高维序列特征的全局建模能力。为解决物联网入侵检测面临的样本类不平衡问题,利用Focal Loss动态缩放模型梯度,自适应降低简单样本的权重,并聚焦于分类困难的类别。最后,在公开的物联网入侵检测数据集ToN_IoT和DS2OS上验证了本文方法的有效性,实验结果表明:FATIDS在ToN_IoT的准确率、精确率、召回率和F1分数4项指标分别为99.60%、97.51%、96.59%和97.02%,在DS2OS四项指标分别为99.47%、99.93%、95.77%和97.42%,本文方法相较其他先进方法实现了更强的检测性能。此外,还进一步验证了重要超参数对本文方法性能的影响。
中图分类号:
- TP183
| [1] | Heidari A, Jabraeil J M A. Internet of Things intrusion detection systems: a comprehensive review and future directions[J]. Cluster Computing, 2022, 1: 1-28. |
| [2] | Kaur B, Dadkhah S, Shoeleh F, et al. Internet of Things (IoT) security dataset evolution: challenges and future directions[J]. Internet of Things, 2023, 22: No.100780. |
| [3] | Khraisat A, Alazab A. A critical review of intrusion detection systems in the Internet of Things: techniques, deployment strategy, validation strategy, attacks, public datasets and challenges[J]. Cybersecurity, 2021, 4(1): No.18. |
| [4] | Alani M M, Awad A I. An intelligent two-layer intrusion detection system for the Internet of Things[J]. IEEE Transactions on Industrial Informatics, 2023, 19(1): 683-692. |
| [5] | Pajouh H H, Javidan R, Khayami R, et al. A Two-layer dimension reduction and two-tier classification model for anomaly-based intrusion detection in IoT backbone networks[J]. IEEE Transactions on Emerging Topics in Computing, 2019, 7(2): 314-323. |
| [6] | Saba T, Sadad T, RehmaN A, et al. Intrusion detection system through advance machine learning for the Internet of Things networks[J]. IT Professional, 2021, 23(2): 58-64. |
| [7] | Albulayhi K, Abu Al-haija Q, Alsuhibany S A, et al. IoT intrusion detection using machine learning with a novel high performing feature selection method [J]. Applied Sciences, 2022, 12(10): No.5015. |
| [8] | Islam N, Farhin F, Sultana I, et al. Towards machine learning based intrusion detection in IoT networks[J]. Computers, Materials & Continua, 2021, 69(2): 1801-1821. |
| [9] | Saba T, Rehman A, Sadad T, et al. Anomaly-based intrusion detection system for IoT networks through deep learning model[J]. Computers and Electrical Engineering, 2022, 99: No.107810. |
| [10] | Abd Elaziz M, Al-qaness M A A, Dahou A, et al. Intrusion detection approach for cloud and IoT environments using deep learning and capuchin search algorithm[J]. Advances in Engineering Software, 2023, 176: No.103402. |
| [11] | Almiani M, Abughazleh A, Al-rahayfeh A, et al. Deep recurrent neural network for IoT intrusion detection system[J]. Simulation Modelling Practice and Theory, 2020, 101: No. 102031. |
| [12] | Jeyanthi D V, Indrani B. IoT-based intrusion detection system for healthcare using RNNBiLSTM deep learning strategy with custom features[J]. Soft Computing, 2023, 27(16): 11915-11930. |
| [13] | 李晓佳, 赵国生, 汪洋, 等. 面向CNN和RNN改进的物联网入侵检测模型[J]. 计算机工程与应用,2023, 59(14): 242-250. |
| Li Xiao-jia, Zhao Guo-sheng, Wang Yang, et al. Improved intrusion detection model of Internet of Things for CNN and RNN[J]. Computer Engineering and Applications, 2023, 59(14): 242-250. | |
| [14] | Altunay H C, Albayrak Z. A hybrid CNN+LSTM-based intrusion detection system for industrial IoT networks[J]. Engineering Science and Technology, an International Journal, 2023, 38: No. 101322. |
| [15] | Dina A S, Siddique A B, Manivannan D. A deep learning approach for intrusion detection in Internet of Things using focal loss function[J]. Internet of Things, 2023, 22: No. 100699. |
| [16] | Lin T Y, Goyal P, Girshick R, et al. Focal loss for dense object detection[J/OL].[2024-04-02]. |
| [17] | Alsaedi A, Moustafa N, Tari Z, et al. TON_IoT telemetry dataset: a new generation dataset of IoT and IIoT for data-driven intrusion detection systems[J]. IEEE Access, 2020, 8: 165130-165150. |
| [18] | Khare S, Totaro M. Ensemble learning for detecting attacks and anomalies in IoT smart home[C]∥3rd International Conference on Data Intelligence and Security (ICDIS), South Padre Island, USA, 2020:56-63. |
| [19] | Vaswani A, Shazeer N, Parmar N, et al. Attention is all you need[C]∥Proceedings of the 31st International Conference on Neural Information Processing Systems (NIPS'17), HookRed, USA, 2017: 6000-6010. |
| [20] | Ioffe S, Szegedy C. Batch normalization: accelerating deep network training by reducing internal covariate shift[C]∥Proceedings of the 32nd International Conference on International Conference,Lille, France,2015: 448-456. |
| [21] | He K, Zhang X, Ren S, et al. Deep residual learning for image recognition[J/OL]. [2024-04-03]. arXiv preprint arXiv:. |
| [22] | Aguiar G, Krawczyk B, Cano A. A survey on learning from imbalanced data streams: taxonomy, challenges, empirical study, and reproducible experimental framework[J]. Machine Learning, 2024,113: 4165-4243. |
| [23] | Wang Z G, Oates T. Imaging time-series to improve classification and imputation[J/OL]. [2024-04-04]. |
| [24] | Lo W W, Layeghy S, Sarhan M, et al. E-GraphSAGE: a graph neural network based intrusion detection system for IoT[C]∥NOMS 2022-2022 IEEE/IFIP Network Operations and Management Symposium, Budapest, Hungary, 2022: 1-9. |
| [25] | Čeponis D, Goranin N. Investigation of dual-flow deep learning models LSTM-FCN and GRU-FCN efficiency against single-flow CNN models for the host-based intrusion and malware detection task on univariate times series data[J]. Applied Sciences, 2020, 10(7): No.2373. |
| [26] | Fauvel K, Lin T, Masson V, et al. XCM: an explainable convolutional neural network for multivariate time series classification[J]. Mathematics, 2021, 9(23): No. 3137. |
| [27] | Zerveas G, Jayaraman S, Patel D, et al. A transformer-based framework for multivariate time series representation learning[C]∥Proceedings of the 27th ACM SIGKDD Conference on Knowledge Discovery & Data Mining, Virtual Event, Singapore, 2021:2114-2124. |
| [28] | Hasan M, Islam M, Islam I, et al. Attack and anomaly detection in IoT sensors in IoT sites using machine learning approaches[J].Internet of Thing, 2019,7: No. 100059. |
| [29] | Benaddi H, Jouhari M, Ibrahimi K, et al. Anomaly detection in industrial IoT using distributional reinforcement learning and generative adversarial networks[J]. Sensors, 2022, 22(21): No. 8085. |
| [30] | Huma Z E, Latif S, Ahmad J, et al. A hybrid deep random neural network for cyberattack detection in the Industrial Internet of Things[J]. IEEE Access, 2021, 9: 55595-55605. |
| [31] | Bai S J, Kolter J Z, Koltun V. An empirical evaluation of generic convolutional and recurrent networks for sequence modeling[J/OL].[2024-04-06]. |
| [1] | 于江波,翁剑成,林鹏飞,孙宇星,柴娇龙. 基于混合Transformer的对外客运枢纽抵站客流预测模型[J]. 吉林大学学报(工学版), 2025, 55(7): 2251-2259. |
| [2] | 戴银飞,周秀贞,范子尧,刘镕源,刘志远,王绍强,杜伟. 车载网络中基于密钥驱动信任机制的身份认证协议[J]. 吉林大学学报(工学版), 2025, 55(5): 1788-1797. |
| [3] | 刘广文,谢欣月,付强,才华,王伟刚,马智勇. 基于时空模板焦点注意的Transformer目标跟踪算法[J]. 吉林大学学报(工学版), 2025, 55(3): 1037-1049. |
| [4] | 蒋磊,王子其,崔振宇,常志勇,时小虎. 基于循环结构的视觉Transformer[J]. 吉林大学学报(工学版), 2024, 54(7): 2049-2056. |
| [5] | 梁礼明,周珑颂,尹江,盛校棋. 融合多尺度Transformer的皮肤病变分割算法[J]. 吉林大学学报(工学版), 2024, 54(4): 1086-1098. |
| [6] | 王德兴,高凯,袁红春,杨钰锐,王越,孔令栋. 基于色彩校正和TransFormer细节锐化的水下图像增强[J]. 吉林大学学报(工学版), 2024, 54(3): 785-796. |
| [7] | 李健,熊琦,胡雅婷,刘孔宇. 基于Transformer和隐马尔科夫模型的中文命名实体识别方法[J]. 吉林大学学报(工学版), 2023, 53(5): 1427-1434. |
| [8] | 何科,丁海涛,赖宣淇,许男,郭孔辉. 基于Transformer的轮式里程计误差预测模型[J]. 吉林大学学报(工学版), 2023, 53(3): 653-662. |
| [9] | 郭晓然,罗平,王维兰. 基于Transformer编码器的中文命名实体识别[J]. 吉林大学学报(工学版), 2021, 51(3): 989-995. |
| [10] | 胡冠宇, 乔佩利. 混沌协方差矩阵自适应进化策略优化算法[J]. 吉林大学学报(工学版), 2017, 47(3): 937-943. |
| [11] | 于赫, 秦贵和, 孙铭会, 闫鑫, 王璇喆. 车载CAN总线网络安全问题及异常检测方法[J]. 吉林大学学报(工学版), 2016, 46(4): 1246-1253. |
| [12] | 胡冠宇, 乔佩利. 基于云群的高维差分进化算法及其在网络安全态势预测上的应用[J]. 吉林大学学报(工学版), 2016, 46(2): 568-577. |
| [13] | 罗智勇, 尤波, 许家忠, 梁勇. 基于三层攻击图的入侵意图自动识别模型[J]. 吉林大学学报(工学版), 2014, 44(5): 1392-1397. |
| [14] | 刘效武, 王慧强, 吕宏武, 安述照. 基于融合的网络安全态势量化感知[J]. 吉林大学学报(工学版), 2013, 43(06): 1650-1657. |
| [15] | 郑明, 沈威, 白天, 刘桂霞, 宫雷光. 基于可扩展标记语言的新型即时通讯系统[J]. , 2012, (06): 1548-1552. |
|
||